Technical Blog
-

Why Mylinking Inline Bypass Switch? The Ultimate Network Bypass Tap for Enterprise Network Security Reliability
In the era of digital transformation, enterprise network security faces severe challenges from cyber threats like DDoS attacks and data breaches. Organizations deploy inline security appliances (Firewalls, IPS, Anti-DDoS, etc.) at core nodes, but their physical serial de...Read more -

Layer 2 Redundancy: STP vs MLAG vs Stacking – Which is the best choice for your network?
In modern network design, Layer 2 redundancy is non-negotiable for ensuring business continuity, minimizing downtime, and avoiding broadcast storms caused by network loops. When it comes to implementing Layer 2 redundancy, three technologies dominate the landscape: Spann...Read more -

sFlow Demystified: Principles, Value, Applications and Integration with Network Packet Broker
In the era of high-speed networks and cloud-native infrastructure, real-time, efficient network traffic monitoring has become a cornerstone of reliable IT operations. As networks scale to support 10 Gbps+ links, containerized applications, and distributed architectures, ...Read more -

What exactly is a Spine-Leaf Network? The Spine-Leaf Network of Underlay Networks
In order to meet the needs of cloud services, the network is gradually divided into Underlay and Overlay. The Underlay network is the physical equipment such as routing and switching in the traditional data center, which still believes in the concept of stability and pro...Read more -

Mylinking™ Network Packet Broker’s Tunnel Encapsulation Stripping: Empowering VTEP in Modern Networks
In the era of cloud computing and network virtualization, VXLAN (Virtual Extensible LAN) has become a cornerstone technology for building scalable, flexible overlay networks. At the heart of VXLAN architecture lies the VTEP (VXLAN Tunnel Endpoint), a critical component t...Read more -

Warm Christmas and New Year 2026 Wishes to Our Valued Partners | Mylinking™ Team
Dear Valued Partners, As the year gradually winds down to a gentle close, we consciously take a moment to pause, reflect, and cherish the journey we’ve embarked on together. Over the past twelve months, we’ve shared countless meaningful moments—from the excitement of lau...Read more -

In-depth Analysis and Application Comparison of TAP and SPAN Network Traffic Data Acquisition Methods
In the fields of network operation and maintenance, troubleshooting, and security analysis, accurately and efficiently acquiring network data streams is the foundation for conducting various tasks. As two mainstream network data acquisition technologies, TAP (Test Access...Read more -

Mylinking™ Network Packet Brokers to Capture, Preprocess and Forward Network Traffic OSI Model Layers to your right tools
Mylinking™ Network Packet Brokers supported Network Traffic Dynamic Load Balancing: The load balance Hash algorithm and session-based weight sharing algorithm according to L2-L7 layer characteristics to ensure that the port output traffic dynamic of load balancing. And M...Read more -

As a skilled Network Engineer, do you understand the 8 common Network Attacks?
Network engineers, on the surface, are just "technical laborers" who build, optimize, and troubleshoot networks, but in reality, we are the "first line of defense" in cybersecurity. A 2024 CrowdStrike report showed that global cyberattacks increased by 30%, with Chinese ...Read more -

What is the Intrusion Detection System(IDS) and Intrusion Prevention System(IPS)?
Intrusion Detection System (IDS) is like the scout in the network, the core function is to find the intrusion behavior and send an alarm. By monitoring network traffic or host behavior in real time, it compares the preset "attack signature library" (such as known virus c...Read more -
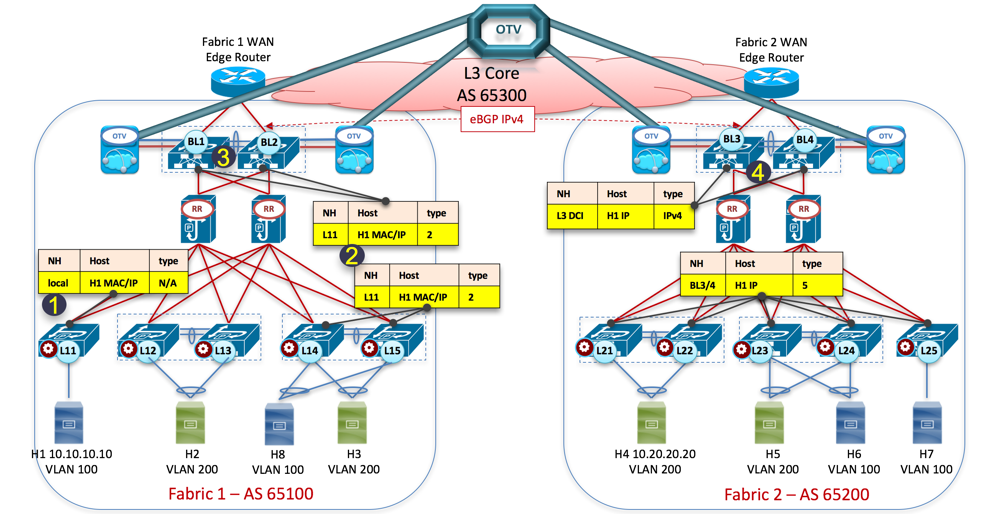
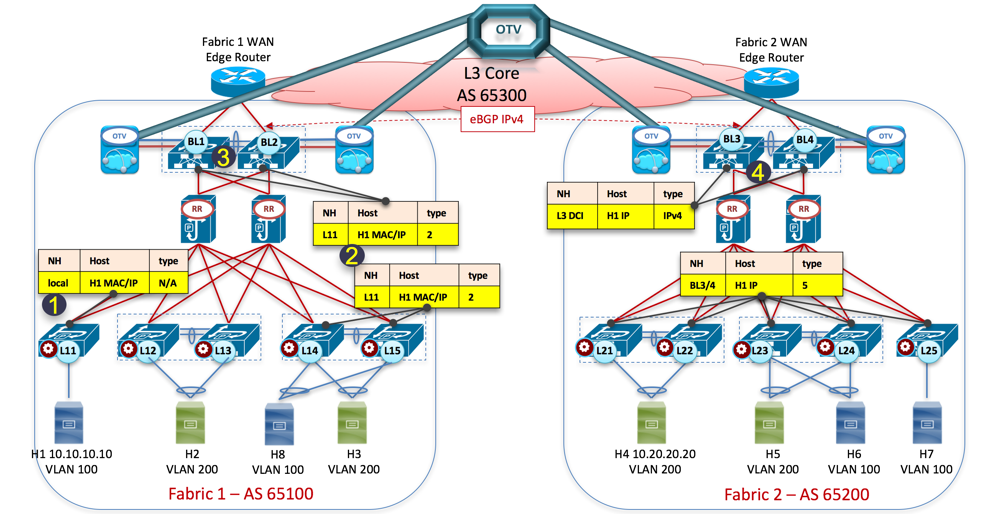
VxLAN(Virtual eXtensible Local Area Network) Gateway: Centralized VxLAN Gateway or Distributed VxLAN Gateway?
To discuss VXLAN gateways, we must first discuss VXLAN itself. Recall that traditional VLANs (Virtual Local Area Networks) use 12-bit VLAN IDs to divide networks, supporting up to 4096 logical networks. This works fine for small networks, but in modern data centers, with...Read more -
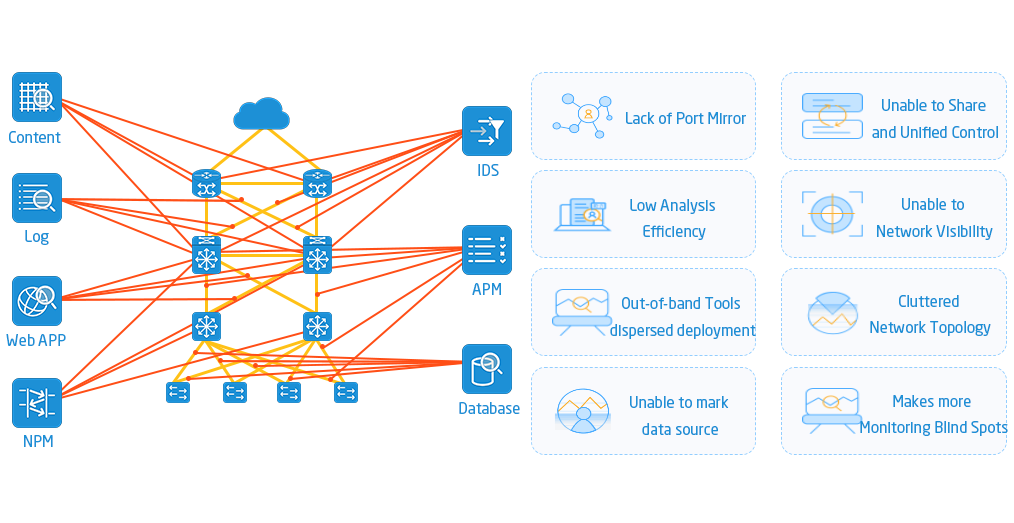
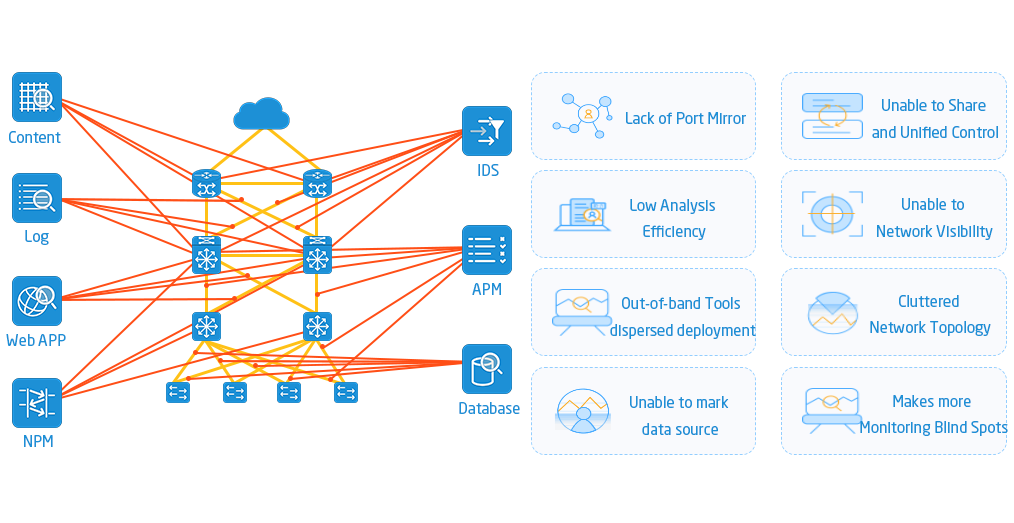
Network Monitoring “Invisible Butler” – NPB: Nework Traffic Management Legend Artifact in the Digital Age
Driven by digital transformation, enterprise networks are no longer simply "a few cables connecting computers." With the proliferation of IoT devices, the migration of services to the cloud, and the increasing adoption of remote work, network traffic has exploded, like t...Read more
-

Tel
-

E-mail
-

Skype
-

Top