Part 1: Core Product Features Summary
Mylinking ML-NPB-M2000 is a 2U modular Network Packet Broker (NPB) integrated with Inline Bypass Switch, designed for high-reliability network security deployment and intelligent traffic processing. It solves the problems of network delay/disruption caused by serial security device failure/maintenance, and supports full-link traffic management, monitoring and security protection. Its core features are categorized as follows:
1. Hardware Specifications
○ Form Factor: 2U 19-inch rackmount, dual power supply (AC-220V/DC-48V optional), max power consumption 300W.
○ Modular Slots: 4 hot-swappable slots for BYPASS/ MONITOR modules (supports mixed configuration).
○ Port Capability: Bypass module (810G SFP+ & 4100GE QSFP28); Monitor module (1610G SFP+ & 4100GE QSFP28); max 2.4Tbps total processing capacity.
○ Management Interfaces: 1RS232 Console, 110/100/1000M RJ45 out-of-band management port.
○ Scalability: Up to 161G/10G inline protection links or 840G/100G links; max 641G/10G or 1640G/100G monitoring ports.
2. Core Functional Capabilities
○ Inline Bypass Protection: Fast bypass switching (<8ms), intelligent heartbeat detection (customizable parameters), automatic bypass for security device failure.
○ Traffic Processing: Basic (replication/aggregation/filtering/labeling) + Advanced (deduplication/masking/slicing/SSL proxy/decryption, L2-L7 protocol identification).
○ Load Balancing: Hash-based load balancing (L2-L4) for security device clusters, session integrity guarantee, dynamic load redistribution.
○ Tunnel Processing: Support stripping/encapsulation of VXLAN/GRE/MPLS/GTP, tunnel protocol automatic identification.
○ Traffic Visibility: Multi-dimensional analysis (DPI deep analysis, flow table/packet analysis, precise fault location), real-time monitoring & alarm, nanosecond-level timestamping.
3. Key Deployment Modes
○ Inline Deployment: Full traffic/specific traffic serial protection, traffic blocking, SSL proxy for encrypted traffic analysis.
○ SPAN Deployment: Out-of-band traffic mirroring, aggregation, distribution for monitoring/analysis systems (IDS/APM/NPM).
○ Hybrid (Inline+SPAN): Inline security protection + out-of-band traffic mirroring, no mutual interference between two modes.
4. Exclusive Core Technologies
○ SpecFlow/FullLink Protection Mode, Fast Bypass Switching, LinkSafeSwitch, WebService Dynamic Policy Forwarding.
○ Customizable Heartbeat Packet Detection, Multi-link Dynamic Load Balancing, Intelligent Traffic Distribution.
Part 2: Product System Applications
All diagrams take the Mylinking ML-NPB-M2000 as the core node, connecting network infrastructure, security devices and monitoring/analysis systems. The product photo is marked as [ML-NPB-M2000 Product Photo] in the layout, and the actual deployment can replace it with the official product physical image.
Diagram 1: Inline Link Serial Security Device Bypass Protection (Core Scenario)
Diagram Name: Inline FW/IPS Failure Automatic Bypass Protection Diagram
Purpose: Zero-interruption protection for FW/IPS failures/maintenance
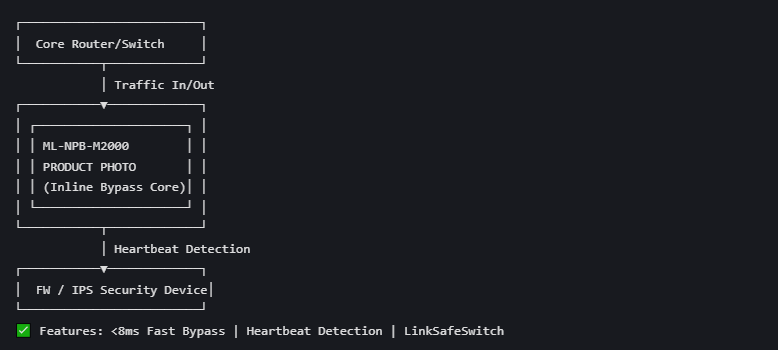
Component Description
Network Layer: Core router/switch (network key node, upstream/downstream traffic entry/exit).
Core Node: ML-NPB-M2000 (integrated Inline Bypass Switch, the core of the whole protection system).
Security Layer: Traditional serial security devices (Firewall/Intrusion Prevention System).
Traffic Flow & Feature Application
1- Normal State: All traffic from core network devices passes through ML-NPB-M2000 to FW/IPS for security check, then returns to the network via the product.
2- Abnormal State: The product’s intelligent bidirectional heartbeat detection identifies FW/IPS failure (crash/overload/maintenance), triggers fast bypass switching (<8ms).
3- Bypass State: Traffic directly forwards between core network devices via ML-NPB-M2000, skipping the faulty FW/IPS, ensuring zero network interruption.
4- Recovery State: The product detects FW/IPS recovery in real time and automatically restores the original traffic path for security protection.
Key Features Applied: Fast Bypass Switching, Customizable Heartbeat Detection, LinkSafeSwitch Technology.
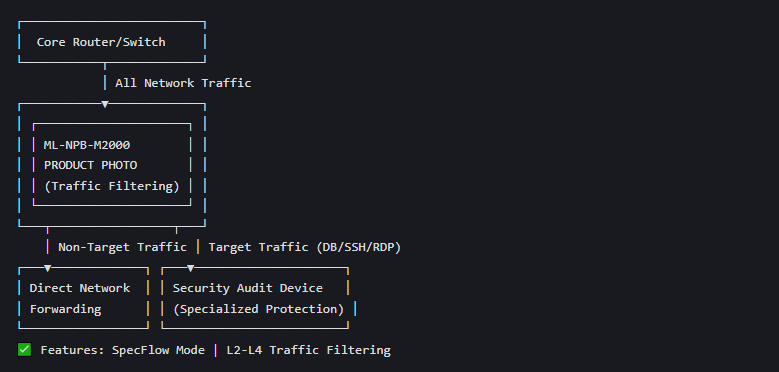
Diagram 2: SpecFlow Specific Traffic Inline Security Protection Diagram
Diagram Name: Policy-Based Specific Traffic Traction & Security Protection Diagram
Purpose: Filter & forward only target traffic to audit devices
Component Description
Network Layer: Core router/switch (all types of traffic input).
Core Node: ML-NPB-M2000 (traffic screening, specific traffic traction).
Security Layer: Specialized security audit devices (for database/SSH/RDP specific traffic, low processing capacity for full traffic).
Traffic Flow & Feature Application
1- The product uses L2-L4 traffic identification (VLAN tag/IP five-tuple/MAC/port) to screen traffic according to pre-configured policies.
2- Non-concerned traffic: Directly forwarded back to the network via the product, no need to pass through security devices (reduces device load).
3- Concerned specific traffic: Traction to the specialized security device for audit/protection, then returns to the network via the product.
4- Real-time heartbeat detection for the security device; automatic bypass if the device fails, ensuring specific traffic protection is not interrupted.
Key Features Applied: SpecFlow Protection Mode, L2-L4 Traffic Filtering, Selective Traffic Protection Technology.
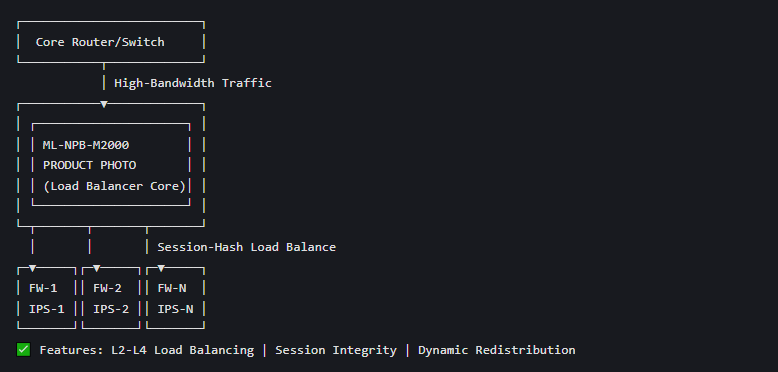
Diagram 3: Load Balanced Inline Security Cluster Protection Diagram
Diagram Name: High-Bandwidth Traffic Load Balancing for FW/IPS Cluster Diagram
Purpose: Distribute 100G traffic across FW/IPS cluster
Component Description
Network Layer: Core router/switch (high-bandwidth peak traffic input, single security device cannot handle).
Core Node: ML-NPB-M2000 (intelligent traffic distribution, load balancing management).
Security Layer: FW/IPS cluster (multiple same security devices deployed in parallel).
Traffic Flow & Feature Application
1- The product receives high-bandwidth traffic from the core network and enables Hash-based load balancing (L2-L4) (based on MAC/IP/port/protocol).
2- Traffic is evenly distributed to each FW/IPS in the cluster for parallel security processing, ensuring session integrity of data flow.
3- The product supports dynamic load redistribution: if a cluster device fails/link is down, traffic is automatically reallocated to other normal devices.
4- The overall processing performance of the security system is improved linearly with the number of cluster devices, adapting to 100G/200G high-bandwidth scenarios.
Key Features Applied: Multi-link Dynamic Load Balancing, Intelligent Traffic Distribution, Fast Bypass for Single Device Failure.
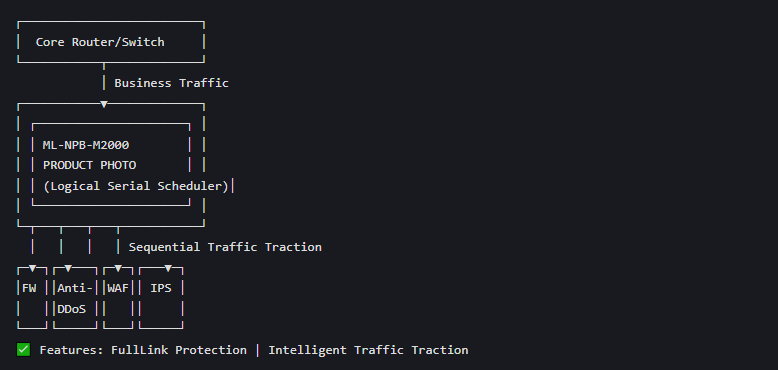
Diagram 4: Multi-Serial Security Device (Physical Serial → Logical Serial) Protection Diagram
Diagram Name: Multi-Security Device Physical Parallel & Logical Serial Traffic Traction Diagram
Purpose: Replace physical serial (single point of failure) with parallel logical serial
Component Description
Network Layer: Core router/switch (key link such as Internet egress/server area).
Core Node: ML-NPB-M2000 (unified traffic scheduling, logical serial management).
Security Layer: Multiple different serial security devices (FW/Anti-DDoS/WAF/IPS, traditional physical serial deployment has single point of failure).
Traffic Flow & Feature Application
1- Traditional deployment: Multiple security devices are physically serially connected, leading to multiple single points of failure and large network delay.
2- New deployment: All security devices are physically parallel to the ML-NPB-M2000; the product implements logical serial traffic traction according to security policies.
3- Traffic passes through each security device in the pre-configured logical order for step-by-step protection, achieving the same effect as physical serial.
4- If one security device fails, the product only bypasses the faulty device, and the rest of the logical serial protection remains effective, reducing single points of failure and improving network reliability.
Key Features Applied: FullLink Protection Mode, Intelligent Traffic Traction, Dynamic Policy Forwarding.
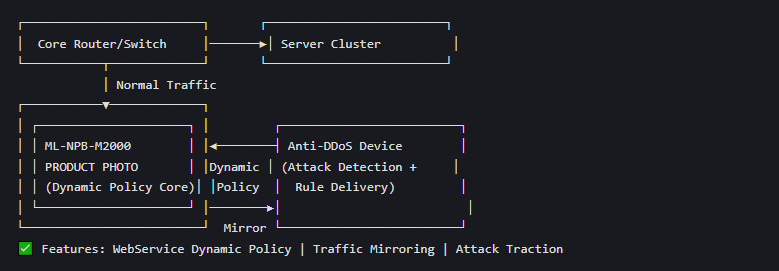
Diagram 5: Dynamic Policy Anti-DDoS Traffic Detection & Protection Diagram
Diagram Name: WebService Dynamic Policy Traction for Anti-DDoS Attack Protection Diagram
Purpose: Real-time attack detection + dynamic traffic traction
Component Description
Network Layer: Core router/switch + Server Cluster (protected target, such as business server IP/segment).
Core Node: ML-NPB-M2000 (wire-speed traffic forwarding, dynamic policy update, traffic traction).
Security Layer: Anti-DDoS attack protection device (real-time attack detection, dynamic policy delivery).
Traffic Flow & Feature Application
1- Normal State: ML-NPB-M2000 forwards full traffic to the server cluster at wire speed, and mirrors all traffic to the Anti-DDoS device for real-time detection (no impact on business traffic).
2- Attack Detected: Anti-DDoS device identifies DDoS attacks on the server IP/segment, generates traffic matching rules, and delivers them to the product via WebService dynamic policy interface.
3- Attack Traction: The product updates the dynamic rule library in real time, tractions the attack traffic to the Anti-DDoS device for cleaning/processing, and normal traffic is still forwarded directly.
4- Attack End: The Anti-DDoS device delivers a policy cancellation command, and the product restores the original full traffic wire-speed forwarding mode.
Key Features Applied: WebService Dynamic Policy Forwarding, Traffic Mirroring, Hardware ASIC Wire-Speed Forwarding, Traffic Blocking.
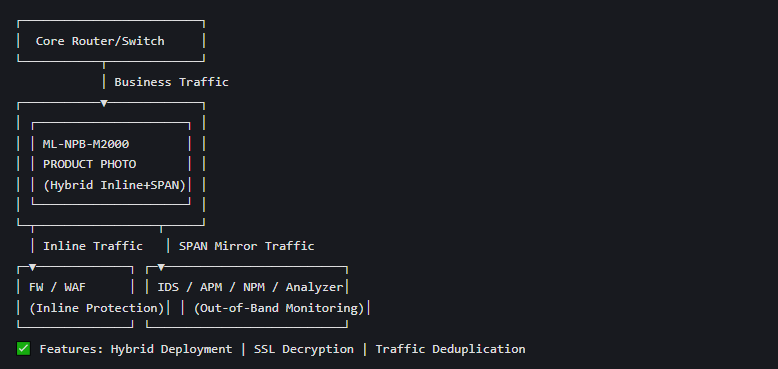
Diagram 6: Hybrid (Inline+SPAN) Inband Protection + Out-of-Band Monitoring Diagram
Diagram Name: Inline FW/WAF Protection + SPAN Out-of-Band IDS/APM Monitoring Diagram
Purpose: Simultaneous inline protection + out-of-band traffic analysis
Component Description
Network Layer: Core router/switch (business traffic input).
Core Node: ML-NPB-M2000 (simultaneously enable Inline and SPAN mode, no mutual interference).
Inband Security Layer: FW/WAF (serial inline protection for business traffic).
Out-of-Band Monitoring Layer: IDS/APM/NPM (traffic analysis, performance monitoring, threat detection).
Traffic Flow & Feature Application
1- Inline Mode: Business traffic passes through the product to FW/WAF for inline security protection, realizing failure bypass and specific traffic traction.
2- SPAN Mode: The product mirrors the full/filtered inline traffic to the out-of-band monitoring system via the Monitor module, without affecting the normal forwarding of inline traffic.
3- The monitoring system performs deep traffic analysis (DPI/flow table/packet analysis), performance monitoring (APM/NPM) and passive threat detection (IDS), and the product supports SSL decryption for mirrored encrypted traffic (HTTPS/TLS) to meet plaintext analysis requirements.
4- The product provides traffic deduplication/masking for mirrored traffic, reducing the processing load of the out-of-band monitoring system.
Key Features Applied: Hybrid Inline+SPAN Deployment, SSL Proxy/Decryption, Traffic Mirroring, Data Deduplication, Traffic Visibility Analysis.
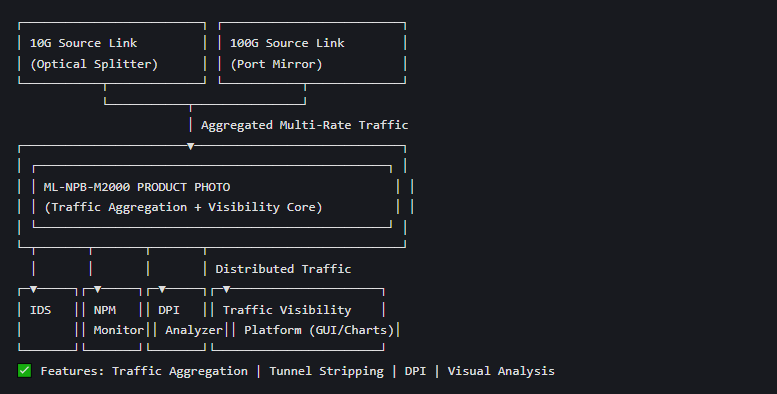
Diagram 7: Network Traffic Unified Scheduling & Visibility Analysis Diagram
Diagram Name: Multi-Link Traffic Aggregation + Unified Scheduling + Visual Analysis Diagram
Purpose: Unify 10G/40G/100G traffic + visual analysis
Component Description
Source Layer: Multi-rate (10G/40G/100G) network source links (Internet egress, server area, core switch), traffic collected via optical splitter/port mirror.
Core Node: ML-NPB-M2000 (unified traffic aggregation, filtering, distribution, preprocessing).
Analysis Layer: Out-of-band security/analysis systems (FW/IDS/NPM/DPI Analyzer).
Visual Layer: Traffic Visibility Platform (product’s built-in GUI, multi-dimensional chart display).
Traffic Flow & Feature Application
1- The product aggregates all traffic from multi-rate source links at wire speed, and preprocesses it (filtering/slicing/deduplication/tunnel stripping).
2- According to pre-configured policies, the product distributes different service traffic to the corresponding out-of-band security/analysis systems (e.g., DDoS traffic to Anti-DDoS, performance data to NPM).
3- The product’s built-in traffic visibility module performs multi-dimensional analysis (DPI deep analysis, flow table/packet analysis, precise fault location) on the aggregated traffic, and displays it in real time via the GUI (pie chart/bar chart/timeline).
4- Support real-time packet capture and historical traffic query for abnormal traffic, helping O&M personnel quickly locate network faults/security threats.
Key Features Applied: Traffic Aggregation/Distribution, Tunnel Stripping, DPI Application Identification, Multi-Dimensional Traffic Visibility, Precise Fault Analysis.
Related Network Packet Broker
Plz visit for more details: https://www.mylinking.com/mylinking-network-packet-broker-plus-inline-bypass-switch-ml-npb-m2000-product/
Related Inline Bypass Switch
Plz visit for more details: https://www.mylinking.com/mylinking-network-packet-broker-plus-inline-bypass-switch-ml-bypass-m2000-product/
Post time: Apr-07-2026