In the era of hyper-connectivity and digital transformation, enterprise network infrastructure faces an unprecedented surge in cyber threats—from DDoS attacks and malicious intrusions to data exfiltration and encrypted traffic vulnerabilities. To safeguard critical business operations, organizations deploy a dense ecosystem of Inline Security solutions at core network nodes, including firewalls (FW), intrusion prevention systems (IPS), anti-DDoS platforms, web application firewalls (WAF), and unified threat management (UTM) tools. Concurrently, Network Monitoring has become non-negotiable for maintaining traffic visibility, troubleshooting faults, and ensuring compliance. However, traditional deployments of standalone Network Packet Broker (NPB) and Inline Bypass Switch solutions create critical operational pain points: single points of failure (SPOF) in inline security chains, unplanned network outages during device maintenance/upgrades, inefficient traffic processing, inability to monitor encrypted SSL/TLS traffic, and performance bottlenecks in high-bandwidth 10/40/100GE environments.
Mylinking addresses these industry-wide challenges with the ML-NPB-M2000—a revolutionary integrated solution that combines the intelligent traffic orchestration capabilities of a next-generation Network Packet Broker (NPB) with the fault tolerance and zero-downtime protection of a premium Inline Bypass Switch, Network Bypass Tap, and Smart Bypass Switch. Engineered for enterprise-grade reliability and performance, the ML-NPB-M2000 delivers a 2.4Tbps full-duplex processing capacity, modular hot-swappable design, 810G SFP+ / 4100GE Bypass modules, 1610GE SFP+ / 4100GE Monitor modules, and advanced traffic processing features including SSL proxy/decryption, traffic deduplication, DPI deep packet inspection, and dynamic policy forwarding. As an all-in-one Inline Bypass Tap and NPB, it redefines Network Security and monitoring by unifying physical and logical inline security deployment, eliminating SPOFs, ensuring zero network downtime, and unlocking granular, real-time traffic visibility for modern enterprises, data centers, and cloud platforms.
This comprehensive technical deep dive explores the ML-NPB-M2000’s core technologies, modular flexibility, intelligent traffic processing capabilities, technical specifications, real-world application scenarios, and competitive advantages—positioning it as the definitive solution for enterprise Network Packet Broker (NPB), Inline Bypass Switch, and network security/monitoring needs.
1. Traditional Network Security & Monitoring: Unresolved Industry Pain Points
Before delving into the ML-NPB-M2000’s groundbreaking capabilities, it is critical to quantify the limitations of traditional Network Security and Network Monitoring deployments—flaws that this integrated Network Packet Broker (NPB) and Inline Bypass Switch is purpose-built to solve. These pain points plague organizations of all sizes, impacting business continuity, operational efficiency, and the return on investment (ROI) of security and monitoring infrastructure, and they center on the disconnect between standalone NPB and inline bypass solutions:
1.1 Single Points of Failure (SPOF) in Inline Security Chains
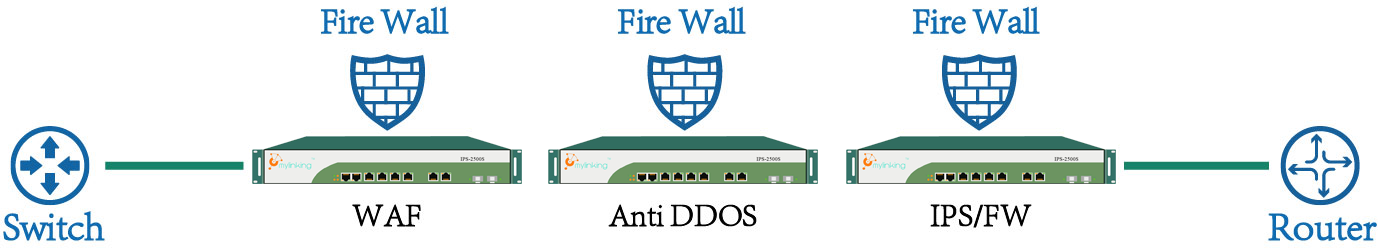
Physical serial deployment of Inline Security devices (FW/IPS/Anti-DDoS) creates cascading SPOFs: a single device failure (overload, crash, firmware corruption) or routine maintenance halts the entire network link, leading to costly unplanned downtime. Traditional Inline Bypass Tap solutions lack the intelligence to integrate with traffic monitoring tools, creating siloed fault protection and visibility.
1.2 Unavoidable Network Outages During Maintenance & Upgrades
Upgrading firmware, replacing hardware, or updating security policies for inline security devices requires manual network disconnection and physical bypass jumpers. These planned outages disrupt critical business applications and erode network reliability—an unacceptable compromise in 24/7 enterprise and data center environments.
1.3 Inefficient Traffic Processing & Visibility Gaps
Standalone Network Packet Broker (NPB) solutions often lack robust inline fault protection, while traditional Smart Bypass Switch tools offer limited traffic processing capabilities (e.g., basic replication/filtering). This results in inefficient traffic distribution, redundant packet capture, blind spots in encrypted traffic monitoring, and inability to tailor traffic inspection to specific security tool requirements—wasting processing resources and reducing monitoring accuracy.
1.4 Encrypted Traffic Monitoring Limitations
SSL/TLS encryption is standard for secure data transmission, but it creates a critical blind spot for Network Monitoring and Inline Security tools. Traditional solutions lack native SSL proxy/decryption capabilities, leaving organizations unable to inspect encrypted traffic for malicious activity without disrupting end-to-end security.
1.5 Performance Bottlenecks in High-Bandwidth Environments
10/40/100GE high-bandwidth links generate massive traffic volumes that overwhelm single security/monitoring devices. Standalone solutions lack dynamic load balancing capabilities to distribute traffic across clustered tools, leading to increased latency, packet loss, and degraded application performance.
1.6 Complex Multi-Device Deployment & Siloed Management
Deploying separate NPB, Inline Bypass Switch, and traffic processing tools requires complex physical cabling, manual configuration, and siloed management. This increases operational overhead for IT teams, delays fault troubleshooting, and creates inconsistencies in traffic policy enforcement across the network.
1.7 Limited Traffic Visibility & Fault Localization
Traditional monitoring solutions offer only basic traffic statistics, with no deep packet inspection (DPI) or visual fault analysis. This leaves organizations unable to quickly identify the root cause of network anomalies, security breaches, or performance issues—extending resolution times and increasing business risk.
These pain points are not just technical nuisances; they directly impact an organization’s ability to maintain a secure, reliable, and visible network. The Mylinking ML-NPB-M2000 solves each of these challenges by unifying Network Packet Broker (NPB) and Inline Bypass Switch functionality into a single, intelligent, and scalable platform—eliminating silos, unlocking zero-downtime operation, and delivering comprehensive Network Security and monitoring.
2. Mylinking ML-NPB-M2000: Integrated NPB + Inline Bypass Switch – A Paradigm Shift in Network Security & Monitoring
The Mylinking ML-NPB-M2000 is the industry’s first enterprise-grade solution to seamlessly integrate the traffic orchestration power of a Network Packet Broker (NPB) with the fault tolerance of a Smart Bypass Switch, Network Bypass Tap, and Inline Bypass Tap. Designed for flexible deployment of serial Inline Security devices and robust Network Monitoring, it is engineered to address the core pain points of traditional deployments while delivering uncompromised performance, scalability, and reliability.
At its core, the ML-NPB-M2000 is a modular, 2U standard 19-inch rackmount device that combines Inline Bypass Switch fault protection with advanced NPB traffic processing—including SSL proxy/decryption, traffic deduplication, DPI, dynamic load balancing, and real-time traffic visibility. Its key design pillars align with the most demanding enterprise and data center requirements:
○ Integration: Unifies NPB, Inline Bypass Switch, Network Bypass Tap, and traffic processing into a single platform, eliminating siloed deployments and operational complexity.
○ Zero-Downtime Operation: Intelligent heartbeat detection and fast bypass switching ensure uninterrupted network communication, even if inline security devices or the ML-NPB-M2000 itself experiences a fault.
○ Modular Scalability: 4 hot-swappable module slots support a mix of Bypass and Monitor modules, enabling custom configuration for 10/40/100GE links and adapting to evolving network needs without full hardware replacement.
○ Advanced Traffic Processing: Native SSL proxy/decryption, DPI for 1800+ application protocols, traffic deduplication, masking, and shaping—unlocking full visibility into encrypted and unencrypted traffic.
○ Dual Deployment Modes: Supports Inline (serial) deployment for security device protection and SPAN (switched port analyzer) deployment for passive Network Monitoring—delivering flexibility for all network key nodes (internet gateways, core switches, data center server farms).
○ Enterprise-Grade Reliability: AC/DC dual power supply, industrial-grade environmental tolerance, and redundant management interfaces ensure 24/7 operation in harsh data center and enterprise environments.
The ML-NPB-M2000 is not just a Network Packet Broker (NPB) or an Inline Bypass Switch—it is a centralized traffic orchestration and protection hub that redefines how organizations deploy Inline Security and Network Monitoring solutions. By unifying these critical functions, it reduces operational overhead, eliminates SPOFs, and delivers the granular traffic visibility and control required for modern digital business.
3. Core Advanced Technologies & Defining Features
The Mylinking ML-NPB-M2000’s industry-leading performance and reliability stem from a portfolio of proprietary and enterprise-proven technologies—each optimized to address the unique challenges of Network Security and Network Monitoring in high-bandwidth environments. These technologies make the ML-NPB-M2000 the most advanced integrated Network Packet Broker (NPB) and Smart Bypass Switch on the market, delivering fault tolerance, traffic intelligence, and seamless manageability. All core features are designed to work in tandem, ensuring a unified, secure, and visible network infrastructure.
3.1 SpecFlow™ & FullLink™ Protection Modes
The ML-NPB-M2000 features two configurable protection modes for Inline Security deployment, aligning with diverse organizational security and traffic processing needs:
○ SpecFlow™ Protection Mode: Enables selective traffic protection by identifying and redirecting only specific traffic types (e.g., RDP, SSH, database traffic, encrypted SSL/TLS traffic) to inline security devices via L2-L4 layer header identification (VLAN tags, MAC/IP addresses, transport layer ports). Unrelated traffic is forwarded directly to the network link, reducing processing load on security tools and minimizing latency.
○ FullLink™ Protection Mode: For scenarios requiring comprehensive security inspection, this mode forwards all network traffic through serial Inline Security devices—ensuring full compliance with enterprise security policies while maintaining the Inline Bypass Switch’s fault tolerance and zero-downtime protection.
Both modes integrate seamlessly with the ML-NPB-M2000’s NPB traffic processing capabilities, enabling granular traffic filtering and policy enforcement for both Inline and SPAN deployments.
3.2 Intelligent & Definable Heartbeat Packet Detection
A cornerstone of the ML-NPB-M2000’s fault tolerance (a core Smart Bypass Switch capability) is its intelligent heartbeat packet detection—a bidirectional soft monitoring technology that eliminates blind spots in inline security device health checks. The ML-NPB-M2000 sends customizable heartbeat packets to the upstream/downstream ports of connected Inline Security devices and validates their return to assess real-time operational status, with key features including:
○ Fully definable heartbeat parameters: Administrators can customize heartbeat transmission intervals, maximum retry counts, and transmission directions to match the latency and reliability characteristics of their security devices.
○ Bidirectional fault detection: The Tx/Rx heartbeat mechanism accurately reflects the full traffic processing path of inline security devices, ensuring no false positives or negatives in fault detection.
○ Instant automatic bypass: If heartbeat packets fail to return (indicating device failure, overload, or disconnection), the ML-NPB-M2000 bypasses the faulty device within <8ms—re-routing traffic directly between network devices to ensure zero network downtime.
○ Seamless automatic recovery: Once the faulty security device resumes normal operation, the heartbeat detection system triggers a seamless reconnection to the security chain—no manual intervention required.
○ Customizable heartbeat packet types: Supports Layer 2, 3, and 4 heartbeat packets, adapting to special inline security devices that cannot forward standard Layer 2 Ethernet frames (e.g., transparent bridge-mode IPS/FW).
This technology ensures the ML-NPB-M2000 acts as a vigilant guardian of the inline security chain, eliminating SPOFs and ensuring continuous network communication—an essential capability for 24/7 enterprise and data center environments.
3.3 Fast Bypass Switching & LinkSafeSwitch™ Technology
To complement intelligent heartbeat detection, the ML-NPB-M2000 integrates Fast Bypass Switching Protection and proprietary LinkSafeSwitch™ Technology—hardware-accelerated features that define its Inline Bypass Tap and Network Bypass Tap capabilities:
○ Sub-8ms bypass switching latency: The ML-NPB-M2000 delivers industry-leading low bypass switching delay, ensuring users experience no perceptible network impact during fault events.
○ Link state preservation: LinkSafeSwitch™ Technology ensures the primary network link’s state remains unchanged during bypass switching, preventing Layer 2/3 topology protocols from re-computing and converging—minimizing network disruption.
○ Fail-open operation: Even if the ML-NPB-M2000 itself experiences a hardware or software fault, it automatically bypasses its own processing layer, maintaining direct connectivity between network devices. This eliminates the ML-NPB-M2000 as a potential SPOF— a critical advantage over standalone Inline Bypass Switch solutions.
3.4 WebService™ Dynamic Policy Forwarding/Issue Technology
A key differentiator of the ML-NPB-M2000’s Network Packet Broker (NPB) functionality is its WebService™ Dynamic Policy Forwarding/Issue Technology—which enables real-time integration with third-party Inline Security and monitoring tools (e.g., Anti-DDoS platforms, SIEM systems). This feature transforms the ML-NPB-M2000 into a centralized traffic control hub, with core capabilities:
○ Real-time dynamic policy updates: Third-party security tools can send traffic matching rules to the ML-NPB-M2000 via a standard WebService API, which updates its traffic traction dynamic rule pool instantaneously—no manual configuration required.
○ On-demand malicious traffic redirection: For example, if an Anti-DDoS device detects an attack on a specific server IP/segment, it triggers the ML-NPB-M2000 to redirect only the malicious traffic to the Anti-DDoS appliance for cleaning—leaving normal traffic unaffected and minimizing latency.
○ Low network dependency: Unlike traditional traffic traction solutions (e.g., BGP route injection), dynamic policy forwarding requires no changes to the underlying network topology—making it easier to implement, maintain, and scale.
○ ASIC-accelerated wire-speed forwarding: The ML-NPB-M2000 uses pure ASIC chip forwarding for up to 100Gbps wire-speed traffic, with no blocking—even when processing hundreds of dynamic policy rules.
3.5 SSL Proxy & Decryption – Unlocking Encrypted Traffic Visibility
One of the most critical Network Monitoring and Inline Security challenges in modern networks is encrypted SSL/TLS traffic. The ML-NPB-M2000 addresses this with native SSL Proxy and SPAN SSL Decryption capabilities—eliminating encrypted traffic blind spots without disrupting end-to-end security:
○ Transparent SSL proxy: Decrypts original encrypted packets, sends the plaintext to inline security/monitoring tools for inspection, and then re-encrypts the data and sends it back to the original network link—ensuring secure data transmission while enabling full traffic inspection.
○ Broad encryption support: Supports TLS1.0, TLS1.2, and SSL3.0, compatible with all standard enterprise encryption protocols.
○ Certificate-based decryption: Loads custom SSL certificates for targeted decryption of specific traffic types, ensuring compliance with data privacy regulations (e.g., GDPR, CCPA).
○ Bypass SSL decryption: For SPAN deployments, decrypts HTTPS encrypted traffic for back-end monitoring/analysis systems—unlocking visibility into malicious activity hidden in encrypted traffic.
This capability is a game-changer for organizations that need to balance secure encrypted data transmission with robust Network Monitoring and Inline Security.
3.6 Multi-Link Dynamic Load Balancing
For high-bandwidth 10/40/100GE environments where a single Inline Security or monitoring device cannot handle peak traffic, the ML-NPB-M2000’s Multi-link Load Balancing and Intelligent Traffic Distribution technologies enable clustered deployment of tools—unlocking linear scalability for processing capacity:
○ Hash-based traffic distribution: Distributes traffic across clustered security/monitoring devices based on L2-L4 layer characteristics (VLAN tags, MAC/IP addresses, port numbers, protocol information)—ensuring session integrity and avoiding packet reordering.
○ Dynamic load adjustment: Real-time monitoring of each device’s processing load, with automatic traffic redistribution to prevent overload and optimize resource utilization.
○ Support for high-density clustering: Enables clustering of up to 1610GE or 8100GE inline security devices, meeting the demands of high-bandwidth core networks, internet gateways, and data center server farms.
○ Dynamic port group membership: Load balancing port groups automatically adapt to link state changes (link UP/DOWN), redistributing traffic to ensure continuous processing—no manual intervention required.
3.7 Comprehensive Remote Management Technology
The ML-NPB-M2000 is designed for seamless remote manageability—critical for large-scale enterprise networks, geographically dispersed data centers, and cloud platforms. As a professional Network Packet Broker (NPB) and Smart Bypass Switch, it supports a full suite of industry-standard management protocols and tools, with role-based access control (RBAC) to ensure administrative security:
○ Graphical management: HTTP/WEB GUI for intuitive real-time monitoring, configuration, fault troubleshooting, and traffic visualization.
○ Command-line management: TELNET/SSH CLI with EasyConfig (basic setup for non-technical administrators) and AdvanceConfig (granular technical configuration for network engineers) modes.
○ Network management integration: SNMP V1/V2C for integration with enterprise network management systems (NMS) and SYSLOG for centralized log collection and analysis.
○ Secure authentication: Password-based authentication, AAA, and TACACS+/RADIUS centralized authorization—ensuring only authorized personnel can access and configure the device.
○ Out-of-band management: A dedicated 1*10/100/1000M RJ45 management interface ensures remote access even if the data plane experiences a fault.
○ Local configuration: RS232 Console interface (115200,8,N,1) for on-site configuration and troubleshooting.
This comprehensive management suite reduces the operational burden on IT teams, streamlines configuration and fault resolution, and ensures consistent policy enforcement across the entire network.
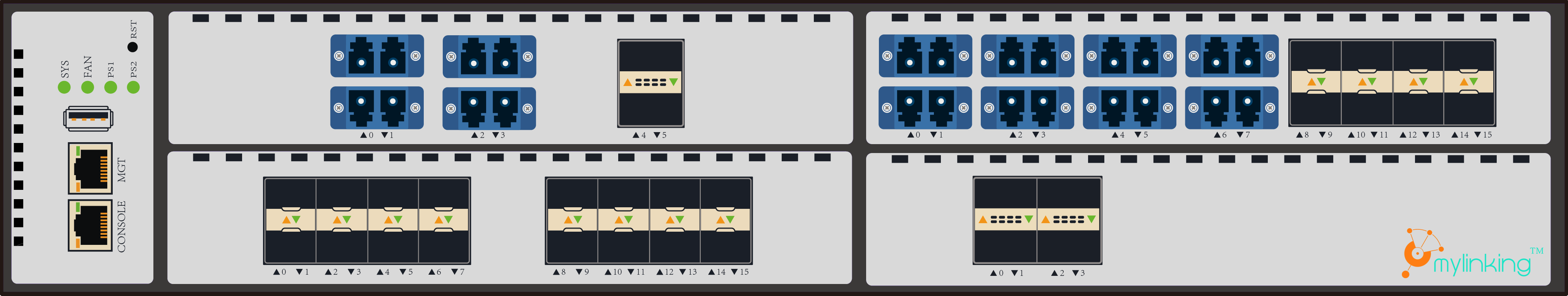
4. Modular Configuration Flexibility – Customizable for Every Network Need
A defining feature of the Mylinking ML-NPB-M2000 is its modular, hot-swappable design—a hallmark of its scalability as an integrated Network Packet Broker (NPB) and Inline Bypass Switch. The device consists of a mandatory chassis (with AC/DC power options) and four universal module slots that support any combination of Bypass and Monitor modules—enabling organizations to tailor the ML-NPB-M2000 to their exact 10/40/100GE link speed, Inline Security protection, and Network Monitoring requirements. All modules support hot-swapping, allowing for maintenance and upgrades without network downtime—further reinforcing the ML-NPB-M2000’s zero-downtime design principle.
4.1 Chassis Specifications (ML-NPB-M2000)
The chassis is the foundation of the ML-NPB-M2000, providing the physical, electrical, and management infrastructure for module integration. Two chassis models are available, differing only in power supply (AC/DC) to adapt to diverse enterprise and data center power environments:
| Chassis Model | Key Technical Specifications |
|---|---|
| ML-NPB-M2000-CHS/AC | 2U 19-inch rackmount; 4 hot-swappable module slots; 1RS232 Console, 110/100/1000M RJ45 mgmt; dual AC-220V power; max 300W power consumption; dimensions 444mm88mm670mm |
| ML-NPB-M2000-CHS/DC | 2U 19-inch rackmount; 4 hot-swappable module slots; 1RS232 Console, 110/100/1000M RJ45 mgmt; dual DC-48V power; max 300W power consumption; dimensions 444mm88mm670mm |
4.2 Bypass Modules – Inline Security Fault Protection
Bypass modules are the core of the ML-NPB-M2000’s Inline Bypass Switch, Network Bypass Tap, and Inline Bypass Tap capabilities, providing serial protection for 10/40/100GE links and integrating directly with the device’s intelligent heartbeat detection and fast bypass switching. All Bypass modules support 1G/10GE (INL-I8XM8X) or 40GE/100GE (INL-I4HM2H) compatibility, ensuring backward and forward compatibility with existing network infrastructure:
| Bypass Module Model | Key Technical Specifications |
|---|---|
| INL-I8XM8X (LM/SM) | 4-way 10GE (1G compatible) link serial protection; 810GE interfaces; 810G SFP+ monitoring ports (no optical modules); single/multimode support |
| INL-I4HM2H (LM/SM) | 2-way 100GE (40GE compatible) link serial protection; 4100GE interfaces; 2100GE QSFP28 monitoring ports (no optical modules); single/multimode support |
4.3 Monitor Modules – Advanced NPB Traffic Processing & Monitoring
Monitor modules power the ML-NPB-M2000’s Network Packet Broker (NPB) functionality, delivering basic and advanced traffic processing for SPAN deployment and Network Monitoring. Two tiers of Monitor modules are available: standard modules (basic traffic processing) and advanced function engine modules (SSL proxy/decryption, traffic deduplication, DPI). All Monitor modules do not include optical modules, allowing organizations to use their existing transceivers for cost efficiency:
| Monitor Module Model | Key Technical Specifications |
|---|---|
| MON-M16X | 16*10GE SFP+ monitoring ports (no optical modules); basic traffic processing (replication/aggregation/filtering) |
| MON-M16X-CN98 | 16*10GE SFP+ monitoring ports (no optical modules); advanced function engine (SSL proxy/decryption, traffic deduplication, DPI) |
| MON-M4H | 4*100GE QSFP28 monitoring ports (no optical modules); basic traffic processing (replication/aggregation/filtering) |
| MON-M4H-CN98 | 4*100GE QSFP28 monitoring ports (no optical modules); advanced function engine (SSL proxy/decryption, traffic deduplication, DPI) |
4.4 Critical Module Configuration Rules
To ensure optimal performance, compatibility, and scalability, the ML-NPB-M2000 follows a set of clear, easy-to-implement module configuration rules—designed to maximize flexibility while avoiding configuration errors:
○ Chassis first: The ML-NPB-M2000 chassis (AC/DC) is a mandatory component; all Bypass/Monitor modules are secondary and must be selected after the chassis.
○ Unlimited slot flexibility: The 4 module slots support any combination of Bypass and Monitor modules (e.g., 4 Bypass, 4 Monitor, 2 Bypass + 2 Monitor)—no slot locking for specific module types.
○ High-density link support: Based on module combinations, the device supports serial protection for up to 161G/10GE optical links or 840G/100GE optical links—meeting the needs of high-bandwidth enterprise and data center networks.
○ High-density monitoring: The device supports up to 641G/10GE monitoring interfaces or 1640G/100GE monitoring interfaces—enabling large-scale clustered monitoring and security device deployment.
○ Hot-swapping enabled: All Bypass and Monitor modules support hot-swapping—allowing for module replacement, upgrade, or maintenance without network downtime or configuration changes.
This modular flexibility makes the ML-NPB-M2000 a future-proof investment—organizations can upgrade their link speeds, security protection, or monitoring capabilities by simply swapping modules (not replacing the entire chassis), reducing total cost of ownership (TCO) and adapting to evolving network needs for years to come.
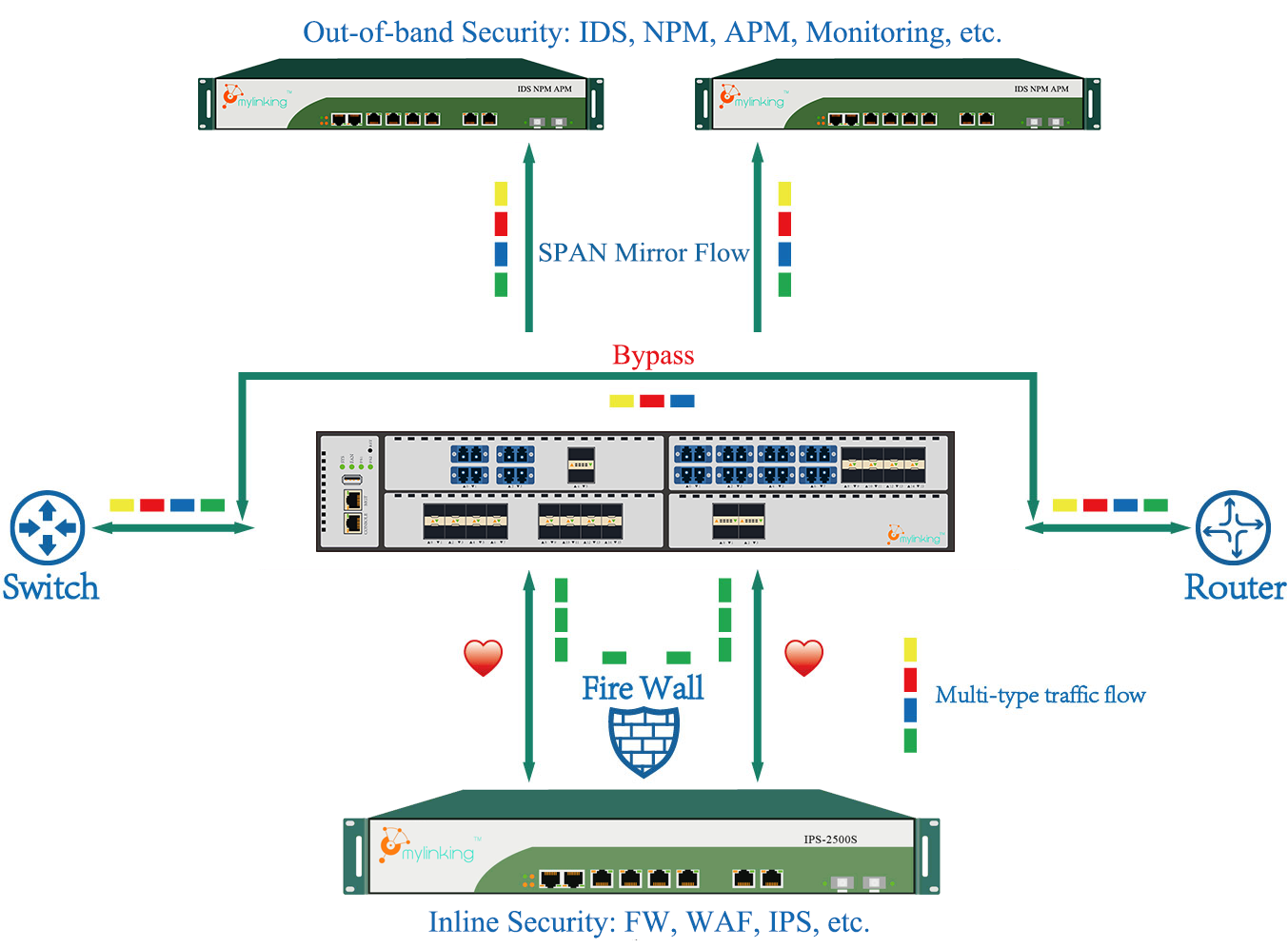
5. Intelligent Traffic Processing Capabilities: Inline & SPAN Deployment Modes
The Mylinking ML-NPB-M2000’s most powerful feature is its dual deployment mode support: Inline (serial) deployment for Inline Security device protection and fault tolerance (leveraging its Inline Bypass Switch, Network Bypass Tap, and Smart Bypass Switch capabilities) and SPAN (passive) deployment for Network Monitoring and advanced traffic processing (leveraging its Network Packet Broker (NPB) functionality). These two modes work independently or in tandem (Inline + SPAN), enabling the ML-NPB-M2000 to address every Network Security and monitoring need at all network key nodes—from internet gateways and core switches to data center server farms and cloud platform links.
5.1 Inline Deployment Mode – Zero-Downtime Inline Security Protection
Inline deployment is the primary mode for Inline Security device protection, where the ML-NPB-M2000 is deployed in series between network devices (routers, switches) and inline security tools (FW/IPS/Anti-DDoS/WAF). In this mode, it acts as a Smart Bypass Switch and Inline Bypass Tap, providing fault tolerance, zero-downtime operation, and selective traffic traction—while integrating basic NPB traffic processing capabilities. Key Inline deployment features include:
○ Specific/All Traffic Inline Protection: SpecFlow™/FullLink™ modes for targeted or comprehensive security inspection (L2-L4 traffic identification).
○ Intelligent Load Balancing: Distribute traffic across clustered security devices to handle high-bandwidth peak traffic (session integrity preserved).
○ <8ms Fast Bypass Switching: Automatic bypass of faulty security devices with minimal network impact (LinkSafeSwitch™ Technology).
○ Bidirectional Heartbeat Detection: Real-time health monitoring of inline security devices with customizable parameters.
○ Traffic Blocking: Intercept illegal/abnormal packets based on 5-tuple matching filter conditions—ensuring network security.
○ Traffic Mirroring: Mirror inline link traffic to out-of-band monitoring tools (IDS/NPM/APM) for passive Network Monitoring—no impact on inline security processing.
○ Transparent SSL Proxy: Decrypt encrypted traffic for security inspection, then re-encrypt for transmission—unlocking encrypted traffic visibility.
5.2 SPAN Deployment Mode – Advanced NPB Traffic Processing for Network Monitoring
SPAN deployment is the passive mode for Network Monitoring, where the ML-NPB-M2000 is deployed to aggregate, process, and distribute traffic from network SPAN ports to monitoring/analysis tools (IDS, NPM, APM, SIEM). In this mode, it acts as a full-featured Network Packet Broker (NPB), delivering basic and advanced traffic processing capabilities—unlocking granular traffic visibility, reducing redundant packet capture, and optimizing monitoring tool performance. The ML-NPB-M2000’s SPAN processing capabilities are unmatched in the industry, with over 30 advanced features split into basic traffic processing and advanced traffic processing:
5.2.1 Basic Traffic Processing (SPAN)
Foundational NPB capabilities for optimizing traffic distribution and basic Network Monitoring:
○ Traffic Replication/Aggregation/Distribution: 1:N replication, N:M aggregation, and precise traffic distribution to monitoring tools—eliminating redundant packet capture.
○ 5-Tuple Traffic Filtering: Granular traffic filtering based on IP/protocol/port 5-tuple, Ethernet type, VLAN tag, and packet characteristics (whitelist/blacklist rules).
○ VLAN Management: VLAN tagging, modification, and deletion—enabling traffic segmentation and localization.
○ Nanosecond Precision Timestamping: NTP-synchronized time stamping of packets (nanosecond accuracy) for fault troubleshooting and log correlation.
○ Tunnel Encapsulation Stripping: Strip VXLAN, GRE, GTP, MPLS, IPIP, and SRV6 tunnel headers—unlocking visibility into tunneled traffic.
○ Packet Slicing: Custom packet slicing (64–960 bytes) to reduce unnecessary data transmission to monitoring tools—lowering bandwidth usage.
○ Tunneling Protocol Identification: Automatic identification of GTP/GRE/VXLAN/PPTP/L2TP/PPPOE/IPIP—enabling policy-based traffic forwarding.
○ Packet Forwarding Priority: Define traffic priority based on service importance—ensuring high-priority packets are forwarded first to avoid monitoring tool alarms.
5.2.2 Advanced Traffic Processing (SPAN)
Enterprise-grade NPB capabilities for solving complex Network Monitoring and security challenges (only available on CN98 advanced function engine Monitor modules):
○ SSL Decryption: Decrypt HTTPS/SSL/TLS traffic for monitoring/analysis (TLS1.0/TLS1.2/SSL3.0 support).
○ Traffic Deduplication: Port/policy-based deduplication of duplicate packets—reducing monitoring tool false alarms and processing load.
○ Data Masking: Policy-based masking of sensitive data fields (e.g., credit card numbers, personal information)—ensuring compliance with data privacy regulations.
○ DPI Deep Packet Inspection: Identify 1800+ application layer protocols (audio/video, gaming, IM, database, email, P2P) with an upgradeable DPI feature library—unlocking application-level traffic visibility.
○ Custom Packet Decapsulation: Strip custom encapsulation fields from the first 128 bytes of packets—adapting to proprietary network protocols.
○ Traffic Shaping: Smooth traffic output to monitoring tools via shaping technology—eliminating packet loss from traffic microbursts.
○ Packet Keyword Matching: Match payload field content and forward/discard associated packets/sessions—enabling targeted threat detection.
○ Long-Lived Connection Offloading: Discard redundant long-lived connection traffic after initial capture—reducing monitoring tool processing load.
○ Tunnel Encapsulation Output: Encapsulate collected traffic into ERSPAN2/GRE/VXLAN/NVGRE tunnels—transmitting traffic to remote monitoring/analysis systems.
○ Tunnel Packet Termination: Configure IP/MAC addresses for traffic input ports to receive tunneled traffic (GRE/GTP/VXLAN) directly—simplifying remote traffic collection.
5.3 Inline + SPAN Hybrid Deployment – Unified Security & Monitoring
The ML-NPB-M2000’s true power is unlocked in Inline + SPAN hybrid deployment, where it provides zero-downtime Inline Security protection (Inline mode) and simultaneous passive Network Monitoring (SPAN mode). In this mode, the device mirrors inline link traffic to out-of-band monitoring tools while protecting inline security devices from failure—delivering a unified Network Security and monitoring solution with no silos, no additional hardware, and no network performance impact. This hybrid mode is the ideal deployment for critical network key nodes (e.g., internet gateways, data center core switches), where both continuous security protection and real-time traffic visibility are non-negotiable.
5.4 Comprehensive Traffic Visibility & Fault Analysis
A key component of the ML-NPB-M2000’s Network Packet Broker (NPB) functionality is its integrated traffic visibility and fault analysis module—a user-friendly graphic interface that delivers multi-dimensional, real-time Network Monitoring and precise fault localization. This module transforms raw traffic data into actionable insights, with three core analysis capabilities:
○ Basic Traffic Analysis: Summary statistics (packet count, unicast/multicast/broadcast distribution, session count, protocol distribution) and real-time traffic trend charts.
○ DPI Deep Analysis: Transport layer protocol proportion, IP traffic ranking, DPI application protocol distribution, and timeline-based traffic analysis (1ms precision) with interactive time sliders.
○ Precise Fault Analysis: Multi-layer fault localization including abnormal overview, flow table-level fault analysis (connection rejection/unresponsiveness), packet-level fault analysis (checksum errors/TTL 0), security fault analysis (DDoS/ARP attacks/firewall blocking), and network fault analysis (switching/routing loops/link interruptions).
○ Traffic Statistical Analysis: Real-time TOPN ranking of IP addresses, application protocols, and traffic sessions—with chart visualization and local file export for compliance and reporting.
This traffic visibility module eliminates the need for standalone monitoring tools, reducing operational complexity and enabling IT teams to quickly identify, troubleshoot, and resolve network and security faults—minimizing downtime and business risk.
6. Comprehensive Technical Specifications of the ML-NPB-M2000
The Mylinking ML-NPB-M2000 is engineered to meet the most stringent technical requirements of enterprise, data center, and cloud platform networks—delivering uncompromised performance, reliability, and scalability as an integrated Network Packet Broker (NPB) and Inline Bypass Switch. Below is a complete breakdown of its enterprise-grade technical specifications, organized by functional category for easy reference:
6.1 Core Network & Interface Specifications
| Parameter | Specification |
|---|---|
| Product Modality | Mylinking ML-NPB-M2000 Network Packet Broker (NPB) + Inline Bypass Switch |
| Form Factor | 2U standard 19-inch rackmount (444mm88mm670mm) |
| Module Slots | 4 hot-swappable universal slots (Bypass/Monitor mix) |
| Max Protected Links | 161G/10GE optical links or 840G/100GE optical links |
| Max Monitoring Interfaces | 641G/10GE or 1640G/100GE |
| Management Interfaces | 1RS232 Console (115200,8,N,1); 110/100/1000M RJ45 out-of-band mgmt |
| Processing Capacity | 2.4Tbps full-duplex (ASIC-accelerated wire-speed forwarding) |
| Bypass Switching Latency | <8ms (industry-leading) |
6.2 Deployment & System Functions
| Function Category | Supported Features |
|---|---|
| Deployment Modes | Inline (serial), SPAN (passive), Inline + SPAN hybrid |
| Inline Mode Functions | SpecFlow™/FullLink™ protection, load balancing, heartbeat detection, fast bypass, traffic blocking/mirroring, SSL proxy |
| SPAN Mode Basic Functions | Traffic replication/aggregation/distribution, 5-tuple filtering, VLAN management, timestamping, tunnel stripping, packet slicing |
| SPAN Mode Advanced Functions | SSL decryption, traffic deduplication, data masking, DPI (1800+ protocols), traffic shaping, keyword matching, long-lived connection offloading |
| Traffic Visibility | Basic analysis, DPI deep analysis, precise fault analysis, statistical analysis (chart visualization/export) |
| Reliability Features | Module hot-swapping, fail-open bypass, interface hot backup (1+1), interface oscillation protection, traffic microburst measurement |
6.3 Management & Authentication
| Management Category | Supported Protocols/Tools |
|---|---|
| Remote Management | HTTP/WEB GUI, TELNET/SSH CLI (EasyConfig/AdvanceConfig), SNMP V1/V2C, SYSLOG |
| Authentication | Password-based, AAA, TACACS+/RADIUS centralized authorization |
| Logging & Reporting | Real-time alarm monitoring, historical alarm records, traffic statistic export |
6.4 Electrical & Environmental Specifications (Industrial-Grade)
| Category | Specification |
|---|---|
| Power Supply | AC-220V or DC-48V (dual power, optional) |
| Power Frequency | AC-50Hz |
| Input Current | AC-3A / DC-10A |
| Max Power Consumption | 300W |
| Working Temperature | 0℃ – 50℃ (32°F – 122°F) |
| Storage Temperature | -20℃ – 70℃ (-4°F – 158°F) |
| Working Humidity | 10% – 95% (non-condensing) |
| Storage Humidity | 5% – 95% (non-condensing) |
These specifications confirm the ML-NPB-M2000 as a high-performance, industrial-grade integrated NPB and Inline Bypass Switch—engineered for 24/7 operation in the most demanding enterprise, data center, and cloud platform environments.
7. Real-World Industry Application Scenarios
The Mylinking ML-NPB-M2000’s dual deployment modes, modular flexibility, and advanced traffic processing capabilities make it suitable for all enterprise network key nodes—from internet gateways and core switches to data center server farms, cloud platform links, and branch office connections. Below are the 10 core real-world application scenarios where the ML-NPB-M2000 delivers the greatest value, addressing specific Network Security and Network Monitoring challenges and leveraging its full capabilities as a Network Packet Broker (NPB), Smart Bypass Switch, Network Bypass Tap, and Inline Bypass Tap:
7.1 Inline Link Series Security Device Protection
○ Challenge: Single inline security device (FW/IPS) failure or maintenance causes network downtime.
○ Solution: Deploy the ML-NPB-M2000 in Inline mode between network devices and security tools—intelligent heartbeat detection and <8ms bypass switching ensure zero downtime if the security device fails or is taken offline for maintenance.
○ Key Benefit: Uninterrupted network communication and 24/7 security protection.
7.2 SpecFlow™ Policy Flow Inline Security Protection
○ Challenge: All traffic is forced through security devices, wasting processing resources and increasing latency.
○ Solution: Use SpecFlow™ mode to redirect only specific traffic types (e.g., database/SSH/encrypted traffic) to security tools—unrelated traffic is forwarded directly.
○ Key Benefit: Reduced security tool load, lower latency, and targeted security inspection.
7.3 Load Balanced Inline Security Protection (High-Bandwidth)
○ Challenge: Single security device cannot handle peak 10/40/100GE traffic, leading to latency/packet loss.
○ Solution: Deploy the ML-NPB-M2000’s dynamic load balancing to cluster multiple security devices—Hash-based traffic distribution ensures session integrity and optimal resource utilization.
○ Key Benefit: Linear scalability for security processing capacity and support for high-bandwidth peak traffic.
7.4 Physical-to-Logical Serial Connection Transformation
○ Challenge: Multiple physical serial security devices create multiple SPOFs and significant latency.
○ Solution: The ML-NPB-M2000 transforms physical serial deployment to physical parallel + logical serial—all security devices connect to the ML-NPB-M2000, which tractions traffic to each tool on demand.
○ Key Benefit: Eliminates multiple SPOFs, reduces latency, and enables maintenance of individual security devices with no network downtime.
7.5 Dynamic Policy-Based Traffic Traction (Anti-DDoS)
○ Challenge: Traditional Anti-DDoS traffic traction (BGP) is complex and requires network topology changes.
○ Solution: Integrate the ML-NPB-M2000 with Anti-DDoS tools via WebService™ dynamic policy forwarding—malicious traffic is redirected to Anti-DDoS tools in real time, with no network changes.
○ Key Benefit: Real-time threat response, low network dependency, and minimal latency for normal traffic.
7.6 Inline + SPAN Hybrid Out-of-Band Security Monitoring
○ Challenge: Need for simultaneous inline security protection and passive Network Monitoring with no additional hardware.
○ Solution: Hybrid Inline + SPAN deployment—ML-NPB-M2000 protects inline security devices while mirroring traffic to out-of-band monitoring tools (IDS/NPM/APM).
○ Key Benefit: Unified security and monitoring, no silos, no additional hardware cost.
7.7 Traffic Deduplication for Monitoring Tool Optimization
○ Challenge: Duplicate packets cause monitoring tool false alarms and increased processing load.
○ Solution: Use the ML-NPB-M2000’s port/policy-based traffic deduplication to remove duplicate packets before they reach monitoring tools.
○ Key Benefit: Reduced false alarms, lower monitoring tool load, and improved analysis accuracy.
7.8 VLAN Tagging for Traffic Anomaly Localization
○ Challenge: Unable to quickly locate the source of network anomalies/security breaches.
○ Solution: Use the ML-NPB-M2000’s VLAN tagging to label traffic from different network nodes—backend tools can trace anomalies to the exact source via VLAN tags.
○ Key Benefit: Fast fault localization, reduced troubleshooting time, and improved network visibility.
7.9 Unified Network Traffic Scheduling (Data Center)
○ Challenge: Disparate 10/40/100GE link traffic is difficult to aggregate and distribute to monitoring/security tools.
○ Solution: Deploy the ML-NPB-M2000 as a centralized traffic scheduler—aggregate all link traffic, filter/slice it, and distribute it to the appropriate tools.
○ Key Benefit: Centralized traffic control, reduced operational complexity, and optimized tool utilization.
7.10 Comprehensive Network Traffic Visibility Analysis
○ Challenge: Lack of real-time, multi-dimensional traffic visibility and fault analysis capabilities.
○ Solution: Use the ML-NPB-M2000’s integrated traffic visibility module—basic/DPI deep analysis and precise fault analysis deliver actionable insights via a user-friendly graphic interface.
○ Key Benefit: Real-time network monitoring, fast fault resolution, and compliance-ready traffic statistics.
8. Competitive Advantages of the Mylinking ML-NPB-M2000
In a crowded market of standalone Network Packet Broker (NPB) and Inline Bypass Switch solutions, the Mylinking ML-NPB-M2000 stands out as the premier integrated Network Security and monitoring platform for enterprise, data center, and cloud networks. Its unique combination of integration, performance, flexibility, and intelligence delivers a competitive edge that no standalone solution can match—making it the top choice for organizations prioritizing network reliability, security, and visibility. Below are the 10 key competitive advantages that define the ML-NPB-M2000:
8.1 Unprecedented Integration: NPB + Inline Bypass Switch in One Platform
The ML-NPB-M2000 is the industry’s first enterprise-grade solution to unify Network Packet Broker (NPB) traffic processing with Inline Bypass Switch fault tolerance—eliminating siloed deployments, reducing physical cabling, and lowering operational complexity. No other solution offers this level of integration, making the ML-NPB-M2000 a one-stop shop for Network Security and Network Monitoring.
8.2 Industry-Leading 2.4Tbps Processing Capacity
With a 2.4Tbps full-duplex ASIC-accelerated processing capacity and support for 10/40/100GE links, the ML-NPB-M2000 matches the performance demands of the most demanding high-bandwidth data center and enterprise core networks—delivering wire-speed forwarding with no blocking, even when processing complex traffic rules.
8.3 Fully Modular & Hot-Swappable Design
4 universal hot-swappable module slots support any combination of Bypass and Monitor modules—enabling custom configuration for every network need and maintenance/upgrades with no network downtime. This modular flexibility makes the ML-NPB-M2000 future-proof, with no hardware obsolescence as network needs evolve.
8.4 Dual Deployment Modes (Inline/SPAN) + Hybrid Inline + SPAN
Support for Inline, SPAN, and hybrid Inline + SPAN deployment modes delivers unrivaled flexibility—adapting to every network key node and use case, from inline security protection to passive monitoring. No standalone NPB or Inline Bypass Switch offers this level of deployment flexibility.
8.5 Native SSL Proxy/Decryption – Eliminating Encrypted Traffic Blind Spots
Native SSL proxy and decryption capabilities (TLS1.0/TLS1.2/SSL3.0) unlock visibility into encrypted traffic— a critical feature missing from most standalone NPB and bypass solutions. This ensures organizations can inspect encrypted traffic for malicious activity without disrupting end-to-end security.
8.6 Sub-8ms Fast Bypass Switching & Fail-Open Operation
Industry-leading <8ms bypass switching latency and fail-open operation ensure zero network downtime—even if inline security devices or the ML-NPB-M2000 itself experiences a fault. This fault tolerance is unmatched by standalone NPB solutions, which lack native bypass capabilities.
8.7 DPI for 1800+ Application Protocols (Upgradeable Library)
Integrated DPI deep packet inspection for 1800+ application layer protocols (with an upgradeable feature library) delivers application-level traffic visibility—enabling targeted security inspection and Network Monitoring for modern application-heavy networks.
8.8 Comprehensive Traffic Visibility & Precise Fault Analysis
An integrated, user-friendly traffic visibility module delivers multi-dimensional basic/DPI deep analysis and precise fault localization—eliminating the need for standalone monitoring tools and reducing operational overhead.
8.9 Seamless Third-Party Integration (WebService™ Dynamic Policy)
WebService™ dynamic policy forwarding enables real-time integration with all third-party Inline Security and monitoring tools (FW/IPS/Anti-DDoS/SIEM)—making the ML-NPB-M2000 vendor-agnostic and compatible with existing security stacks (best-of-breed deployment).
8.10 Enterprise-Grade Reliability & Industrial-Grade Environmental Tolerance
AC/DC dual power supply, module hot-swapping, interface hot backup, and industrial-grade temperature/humidity tolerance ensure 24/7 operation in harsh data center and enterprise environments—delivering the reliability required for critical network infrastructure.
So, in an era where network downtime costs enterprises thousands (or millions) of dollars per minute, and cyber threats grow more sophisticated by the day, the Mylinking ML-NPB-M2000 is more than just a Network Packet Broker (NPB) or an Inline Bypass Switch—it is a strategic investment in Network Security, reliability, and visibility. By unifying NPB traffic processing with the fault tolerance of a Smart Bypass Switch, Network Bypass Tap, and Inline Bypass Tap, it solves the core pain points of traditional standalone deployments: eliminating SPOFs, ensuring zero network downtime, unlocking encrypted traffic visibility, and delivering granular, real-time Network Monitoring for modern enterprise, data center, and cloud networks.
With its 2.4Tbps processing capacity, modular hot-swappable design, dual Inline/SPAN deployment modes, native SSL proxy/decryption, DPI deep packet inspection, and comprehensive traffic visibility, the ML-NPB-M2000 is the definitive integrated Network Security and monitoring solution for organizations that demand uncompromised performance, scalability, and reliability. It is engineered to meet the needs of modern digital business—where 24/7 network availability, robust security, and full traffic visibility are non-negotiable.
Take the Next Step with Mylinking ML-NPB-M2000
Ready to transform your Network Security and Network Monitoring deployments, eliminate silos, and ensure zero network downtime?
○ Explore the Mylinking ML-NPB-M2000 product page: https://www.mylinking.com/mylinking-network-packet-broker-plus-inline-bypass-switch-ml-npb-m2000-product/
○ Contact the Mylinking technical team: Customize a modular configuration that matches your exact 10/40/100GE link speed, Inline Security, and Network Monitoring requirements.
○ Request a live demo: See the ML-NPB-M2000’s integrated NPB + Inline Bypass Switch capabilities in action—including zero-downtime bypass, SSL decryption, DPI, and traffic visibility—for your specific network scenario.
○ Get a quote: Learn how the ML-NPB-M2000 reduces your total cost of ownership (TCO) by eliminating standalone NPB and bypass hardware, reducing operational overhead, and delivering a future-proof network solution.
With the Mylinking ML-NPB-M2000, you can deploy a robust, scalable, and unified Network Security and monitoring stack—without compromising network reliability, performance, or visibility.
Post time: Mar-26-2026