Mylinking™ Network Packet Broker plus Inline Bypass Switch ML-BYPASS-M2000
Bypass module: 8*10G SFP+ & 4*100GE, Monitor module: 16*10GE SFP+ & 4*100GE, Max 2.4Tbps
1-Overviews
With the rapid development of the Internet, the threat of network information security is becoming more and more serious, so a variety of information security protection applications are used more and more widely. Whether it is traditional access control equipment (firewall) or a new type of more advanced protection means such as intrusion prevention system (IPS),Unified threat management platform (UTM), Anti-denial service attack system (Anti-DDoS), Anti-spam Gateway, Unified DPI Traffic Identification and Control System, and many security devices are deployed in series in the network key nodes, the implementation of the corresponding data security policy to identify and deal with legal / illegal traffic. At the same time, however, the computer network will generate a large network delay or even network disruption in the case of fail over, maintenance, upgrade, equipment replacement and so on in a highly reliable production network application environment, users cannot stand it.
ML-BYPASS-M2000 Mylinking™ Network Packet Broker plus Inline Bypass Switch is researched and developed to be used for flexible deployment of various types of serial security equipment while providing high network reliability.
By deploying Mylinking™ Network Packet Broker plus Inline Bypass Switch:
●Users can flexibly install/uninstall security protection devices without affecting or interrupting the existing network;
● It has an intelligent health detection function to monitor the normal working status of connected security devices in real time. Once a connected security device malfunctions, the protector will automatically bypass to maintain normal network communication.
●Selective traffic protection technology can be used to deploy specific traffic scrubbing security equipment, encryption-based auditing equipment, etc. It effectively implements inline access protection for specific traffic types, offloading the traffic processing load of inline devices.
● Load balancing traffic protection technology can be used to deploy secure in-line devices in clusters to meet the needs of in-line security protection under high bandwidth pressure environments.
●It has SSL proxy capabilities, meeting the monitoring and analysis requirements of security protection devices for plaintext data content.
● It possesses basic traffic processing capabilities such as traffic replication, aggregation, filtering, and labeling, as well as advanced traffic processing capabilities such as deduplication, masking, application layer protocol identification, and traffic shaping.

2- Mylinking™ Network Packet Broker plus Inline Bypass Switch Advanced Features and Technologies
Mylinking™ “SpecFlow” Protection Mode and “FullLink” Protection Mode Technology
Mylinking™ Fast Bypass Switching Protection Technology
Mylinking™ “LinkSafeSwitch” Technology
Mylinking™ “WebService” Dynamic Policy Forwarding/Issue Technology
Mylinking™ Intelligent Heartbeat Packet Detection Technology
Mylinking™ Definable Heartbeat Packets Technology
Mylinking™ Multi-link Load Balancing Technology
Mylinking™ Intelligent Traffic Distribution Technology
Mylinking™ Dynamic Load Balancing Technology
Mylinking™ Remote Management Technology(HTTP/WEB, TELNET/SSH, “EasyConfig/AdvanceConfig” Characteristic)
3- Mylinking™ Network Packet Broker plus Inline Bypass Switch Configuration Guide

As shown in the diagram above, the entire unit consists of four modular slots:
The SLOT1, SLOT2, SLOT3, and SLOT4 module slots can all accommodate BYPASS protection port modules or MONITOR port modules with different rates and port numbers. By replacing different models of modules, it is possible to support BYPASS protection for multiple 10G/40G/100G links, as well as the deployment of Inline Bypass monitoring equipment for multiple 10G/40G/100G links.
Note: Both the BYPASS module and MONITOR module support hot-swapping.
3.1- Module Specifications List
| Product Model |
Functional Parameters |
| Chassis | |
| ML-BYPASS-M2000-CHS/AC | 2U standard 19-inch rackmount; maximum power consumption 300W; modular BYPASS protector main unit; 4 module slots; 1*RS232 Console interface, 1*10/100/1000M RJ45 interface with external network management; dual power supply AC-220V; |
| NT-BYPASS-M2000-CHS/DC | 2U standard 19-inch rackmount; maximum power consumption 300W; modular BYPASS protector main unit; 4 module slots; 1*RS232 Console interface, 1*10/100/1000M RJ45 interface with external network management; dual power supply DC-48V; |
| BYPASS Module | |
| INL-I8XM8X(LM/SM) | Supports 4-way 10GE (compatible with 1G) link serial connection protection, with a total of 8*10GE interfaces; supports 8*10G SFP+ monitoring ports (excluding optical modules). |
| INL-I4HM2H (LM/SM) | Supports 2-way 100GE (40GE compatible) link serial protection, with a total of 4*100GE interfaces; supports 2*100GE QSFP28 monitoring ports (excluding optical modules). |
| MONITOR Module | |
| MON-M16X | 16*10GE SFP+ monitoring ports (excluding optical modules); |
| MON-M16X-CN98 | 16*10GE SFP+ monitoring ports (optical module not included); equipped with an advanced function engine, supporting advanced traffic processing functions such as bypass SSL decryption, SSL proxy, and traffic deduplication; |
| MON-M4H | 4*100GE QSFP28 monitoring ports (optical modules not included); |
| MON-M4H-CN98 | 4*100GE QSFP28 monitoring ports (optical modules not included); equipped with an advanced function engine, supporting advanced traffic processing functions such as bypass SSL decryption, SSL proxy, and traffic deduplication; |
3.2- Module Selection Rules
Based on the different protected links and monitoring equipment deployment requirements, you can flexibly choose different module configurations to meet your actual environment needs; please follow these rules when selecting:
1) The chassis assembly is a mandatory component and must be selected before choosing any other modules. Please also select the appropriate power supply method (AC/DC) according to your needs.
2) The unit supports a maximum of 4 module slots; you cannot select more modules than the number of slots for configuration. Based on the flexible combination of different module models, the unit can support serial protection for up to 16 10GE/GE links or 8 100GE/40GE links.
4- Intelligent Traffic Processing Abilities
4.1- Inline Deployment

Specific Traffic Inline Protection
It supports Inline(serial) protection mode for specific traffic types in any inline link. To forward some user-specified traffic types on the inline link to the Inline Security device for processing, and the rest traffic is forwarded directly without flowing through the Inline Security device. At the same time, it performs real-time monitoring on the running state of Inline Security device. Once the abnormal traffic processing state found, it will be bypassed from the traffic transmission path automatically to ensure the continuity of network service.

All Traffic Inline Protection
It supports Inline(serial) protection mode for all traffic types in any inline link. To transmit all the traffic in the inline link to the Inline Security device for processing, and monitor the running state of the Inline Security device in real time. Once the abnormal traffic processing state found, it will be bypassed from the traffic transmission path automatically to ensure the continuity of network service.
Load Balance
It has intelligent traffic load balancing capability. When the processing performance of a single Inline Security device is not enough to deal with the inline link communication traffic, it can allocate the inline link traffic to N Monitor interfaces by configoring a load balancing group. According to the MAC, IP information, port number, protocol and other information, it performs optional Hash algorithm load balancing output, so that the inline link traffic is evenly distributed to multiple inline security tools for cluster processing, which effectively improves the overall processing performance of the inline security tools. In order to adapt to the requirements of high bandwidth and large traffic application scenarios.

Heartbeat Packet Detection
It supports Tx and Rx heartbeat detection packets through the uplink and downlink of connected inline security devices, and detects the inline tools working status and whether the traffic processing process is normal. The bidirectional heartbeat packet detection mechanism can more accurately reflect the current working state of the inline security device, and more effectively ensure the normal operation of the network.
It can customize the heartbeat parameters of any inline security device, such as heartbeat Tx interval time, maximum heartbeat retry times, heartbeat Tx direction, etc. It can detect and judge the fault state of inline security devices in time, and realize fast bypass switching of protection links.
The heartbeat detection packets are default Ethernet layer 2 frames. When the transparent Layer 2 bridge mode (such as IPS/FW) is deployed, the layer 2 Ethernet frames will be forwarded normally without blocking or dropping. At the same time, it can also support custom Ethernet layer 2, layer 3 and layer 4 heartbeat detection packets to adapt to some special inline security devices can not normally forward ordinary Ethernet layer 2 frames.
Based on the above mechanism, users can realize the service level health detection effect of connected security devices, so that it can ensure the normal work of security services more effectively.

Bypass Switching
It supports very low bypass switching delay (<8ms), and users can hardly feel the impact on the network when the device performs bypass switching. At the same time, the device-specific Link switching technology can ensure that the link state of the primary link is not affected during the bypass switching. This technology will ensure that the bypass switching is more secure, and will not cause the layer 2 / Layer 3 topology protocol of the protected links to re-compute and converge, so as to minimize the impact on the user network during the switching.

Traffic Blocking
When the security device detects illegal or abnormal session connections in the traffic and needs to block them in time, the device can intercept any specified packets in the up/down traffic of the inline link based on the tuple matching filter conditions to ensure the safe operation of network services.

Traffic Mirror
In addition to the traffic protection of the inline link and the Inline Security device (such as IPS, WAF), any SPAN mirrored traffic can also be output to the SPAN security monitoring system (such as IDS, APT), so as to meet the deployment requirements of the SPAN monitoring of traffic data or traffic testing and verification.

SSL Proxy
Through the SSL proxy function, the original encrypted packet is decrypted and sent to the inline security protection system, and then the decrypted data is restored and sent back to the original link, so as to provide the decrypted data to the inline security protection system without affecting the transmission of encrypted data on the original link of the user, and realize the monitoring and analysis of the encrypted data by the analysis system.
4.2- SPAN Deployment

Network Traffic Replication
It supports Inline(serial) protection mode for specific traffic types in any inline link. To forward some user-specified traffic types on the inline link to the Inline Security device for processing, and the rest traffic is forwarded directly without flowing through the Inline Security device. At the same time, it performs real-time monitoring on the running state of Inline Security device. Once the abnormal traffic processing state found, it will be bypassed from the traffic transmission path automatically to ensure the continuity of network service.

Network Traffic Aggregation
The original input traffic and pre-processed traffic can be copied to N channel signal according to 1 channel signal or copied to M channel signal after N channel signal aggregation at GE, 10GE, 40G and 100G line speed forwarding, which perfectly solves the needs of deploying more than two multi-port listening bypass devices in the network at the same time.

Data Distribution/Forwarding
Classified the incoming metdata accurately and discarded or forwarded different data services to multiple interface outputs according to user’s predefined rules.

Packet Data Filtering
The input data traffic can be classified accurately, and different data services can be whitelist or blacklist rules, and multiple interface outputs can be discarded or forwarded. It supports flexible combination based on Ethernet type, vlan tag, IP five-tuple, TCP identifier, packet characteristics and other elements to further meet the deployment requirements of various network security equipment, protocol analysis, signaling analysis, and other traffic monitoring.

Load Balance
The load balancing of optional Hash algorithm can be carried out according to the inner and outer layer characteristics of L2-L4 to ensure the session integrity of the data flow received by the SPAN monitoring device. When the link state changes, the members of the offloading port group can exit (link DOWN) or join (link UP) flexitively, and the offloading group can automatically redistribute the traffic to ensure the dynamic load balancing of the output traffic of the port.

VLAN Tagged
VLAN Untagged
VLAN Replaced
Supported the matching of any key field in the first 128 bytes of a packet. The user can customize the offset value and key field length and content, and determine the traffic output policy according to the user configuration.

Time Stamping
Supported to synchronize the NTP server to correct the time and write the message into the packet in the form of a relative time tag with a timestamp mark at the end of the frame, with the accuracy of nanoseconds

Tunnel Encapsulation Stripping
Supported the VxLAN, VLAN, GRE, GTP, MPLS, IPIP header stripped in the original data packet and forwarded output.
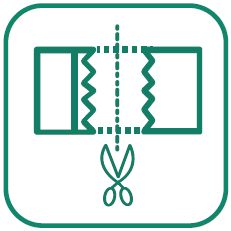
Data/Packet Slicing
It supports packet slicing the original data based on the policy-level traffic input interface and output interface (64, 96, 128, 160, 192, 224, 256, 288, 320, 384, 512, 640, 768, 896, 960 bytes are optional), and the traffic output policy can be implemented according to the user configuration.

Tunneling Protocol Identify
Supported automatically identify various tunneling protocols such as GTP / GRE / VxLAN / PPTP / L2TP / PPPOE / IPIP. According to the user configuration, the traffic output strategy can be implemented according to the inner or outer layer of the tunnel

Packet Forwarding Priority
It supports the definition of priority of data packets according to the importance of the service at the incoming port, and the high-priority packets are forwarded preferentially at the output. After the high-priority packets are forwarded, other medium-and low-priority packets are forwarded. Avoid analysis system alarm caused by missing important data packets.

Abnormal Alarming
It supports real-time monitoring alarm and historical alarm records of interface traffic trends based on threshold setting. It supports real-time monitoring alarms and historical alarm records based on the health status of device hardware (cpu, memory, temperature, fan, power supply, etc.).

Interface Hot Backup
It supports input interface 1+1 primary/standby configuration, output interface 1+1 primary/standby configuration, and load balancing group N+1 primary/standby configuration to achieve high reliability in the process of traffic from input to output.

Traffic Microburst Measurement
It can detect the occurrence time, duration and burst rate of traffic micro-burst in real time, and provide historical measurement record retention, which provides quantifiable and observable means and basis for operation and maintenance troubleshoot and packet loss detection.

Interface Oscillation Protection
It supports the detection and protection of link up/down oscillation events of any interface, so as to avoid the loss of input and output traffic caused by frequent link up/down of interfaces, and improve the stability of traffic collection and forwarding.

Tunnel Encapsulation Output
It supports ERSPAN2, GRE, VXLAN, NVGRE type tunnel encapsulation of any collected traffic and output to meet the application requirements of transmission of collected traffic to remote analysis system.

Tunnel Packet Termination
It supports the tunnel message termination function. This function allows for configuring IP addresses/mask and MAC addresses at the traffic input port. It enables the direct transmission of the traffic that needs to be collected in the user network through tunnel encapsulation methods such as GRE, GTP, and VXLAN to the device's collection port.

SPAN SSL Decryption
Supported loading the corresponding SSL certificate decryption. After the decryption of HTTPS encrypted data for the specified traffic, it will be forwarded to the back-end monitoring and analysis systems as required. Supported TLS1.0, TLS1.2 and SSL3.0

Data/Packet De-duplication
Supported port-based or policy-level statistical granularity to compare multiple collection source data and repeats of same data packet at a specified time. Users can choose different packet identifiers (dst.ip, src.port, dst.port, tcp.seq, tcp.ack, dst.mac, src.mac, vlan.id)

Classified Date Masking
Supported policy-based granularity to replace any key field in the raw data in order to achieve the purpose of shielding sensitive information. According to user configuration, the traffic output policy can be implemented.

APP Layer Protocol Identify
It supports identification, output and discard of Application Layer Protocols based on DNS/URL matching mode. DPI feature library can be integrated to recognize, output and discard no less than 1800 kinds of application protocol features (such as audio and video, game, instant messaging, database, email, P2P, etc.), and the DPI feature library can be upgraded and updated. If there are special needs, secondary development can also be carried out.

Packet User-defined Decapsulation
It supports the function of self-defined packet unencapsulation, which can strip the encapsulation fields and contents at any position of the first 128 bytes of the packet and output it.

Traffic Shapping
At the same time, traffic shaping technology is used in the output interface to output the data flow smoothly to the analysis tool, which fundamentally solves the packet loss phenomenon caused by micro-burst and avoids the abnormal alarm caused by the loss of traffic in the analysis system.

Packet Keyword Matching
After any field content in the payload part of the packet is matched and hit, the associated packet or session flow is forwarded and output or discarded to meet the preprocessing requirements of specific traffic data.

Tunnel Encapsulation Stripping
It supports the output of VXLAN, MPLS, GRE, SRV6, FABRICPATCH, GENEVE and other packet headers in the original data packet after stripping.

Long-lived Connection Offloading
According to the user's needs, any session flow can be forwarded and output according to the number of transmitted bytes and the number of transmitted packets, and the subsequent session flow can be discarded, so as to meet the requirements of the back-end analysis system in some specific scenarios, which only needs to obtain a part of the traffic of the session flow, reduce the pressure of traffic analysis and improve the efficiency of the analysis system.

Traffic Statistical Analysis
It supports the statistics of the components of any input interface traffic, and can display its traffic trend size, traffic size/proportion TOPN of IP address, traffic size/proportion TOPN of application protocol category, traffic size/proportion TOPN of application protocol name and traffic session information in the form of charts in real time, and provides the export of statistical results to local files. Thus, users can more clearly grasp the composition structure of any collected traffic, and provide the most direct data support basis for customing traffic strategies and changing business requirements.

Traffic Visibility - Basic Data Analysis
The basic analysis module of traffic visualization detection function can show the basic information of captured target traffic data, such as packet count, unicast/multicast/broadcast packet distribution, session connection number, packet protocol distribution, and captured traffic size.

Traffic Visibility - DPI Deep Analysis
The DPI deep analysis module of the traffic visibility detection function can conduct in-depth analysis of the captured target traffic data from multiple perspectives, and present detailed statistics in the form of graphs and tables.

Traffic Visibility - Traffic Proportion Analysis
● Transport layer protocol proportion analysis: such as TCP, UDP, ICMP, IGMP, ARP and other packet proportion and traffic statistics and pie chart display
● IP traffic proportion analysis: such as traffic statistics generated by different IP addresses, IP-based traffic ranking TOP N and bar chart display
● DPI application proportion analysis: such as HTTP, QQ, FTP and other application protocols, the number of bytes, communication traffic statistical distribution and pie chart display

Traffic Visibility - Traffic Timeline Analysis
According to different filtering conditions, such as IP, port, transport layer protocol, application layer protocol and other specified content, the current target capture traffic data can be analyzed and presented based on the sampling time, and the traffic size and trend can be queried by moving the time slider and statistical granularity scaling, and the accuracy can reach up to 1 millisecond.

Traffic Visibility – Flow Table Analysis
According to different filter conditions, such as flow ID, IP, port, transport layer protocol, application layer protocol and other specified content, the current target captured traffic data can be analyzed and counted based on the session flow mode, that is, the detailed presentation of session flow information, including the five-tuple information of each flow, the type of carrying application, the number and bytes of packet transmission, and the associated data flow. And has a ranking display based on the above information. Based on this information, users can easily pick up the traffic types they care about, which provides the most direct basis for users to formulate traffic forwarding policies.

Traffic Visibility – Packet Analysis
Based on different filtering criteria, such as packet ID, IP, port, transport layer protocol, application layer protocol and other specified content, the captured target traffic data can be provided with a per-packet level analysis presentation, including:
● Analysis of packet collection timestamp
● Key packet information analysis, such as sip, dip, smac, dmac, protocol, flag, TTL, message length, key events
● Packet transmission path analysis and animation display, such as: forwarding times, forwarding delay, forwarding type (routing, switching, firewall, load balancing, NAT)
● Packet information summary and detailed structure display
● Analysis of the number of repeated packet collection

Traffic Visibility – Precise Fault Analysis
The fault analysis module of the traffic visibility detection function can provide different visual fault analysis positioning for the captured target traffic data, including:
● Abnormal overview, such as: network service analysis results, abnormal event analysis results, network process based on behavior analysis (such as the number of routing devices, NAT devices, firewall devices, load balancing devices passed by the packet transmission)
● Failure analysis at the flow table level, such as abnormal event types (connection rejected/connection unresponsive/connection no data transmission/connection half-open/session route unreachable, etc.), ● Packet-level failure analysis, such as: type of abnormal event (packet checksum error /TTL 0/ unreachable error /FCS checksum error, etc.), detailed description of abnormal information, and details of associated data flow
● Security fault analysis, such as: abnormal event type (DDOS attack/firewall blocking /ARP attack/UDP flood/ SYN FLOOD, etc.), detailed description of abnormal information, and details of associated data flow
● Network fault analysis, such as: abnormal event type (switching loop/routing loop/path unreachable/link interruption, etc.), detailed description of abnormal information, and details of associated data flow
5- Mylinking™ Network Packet Broker plus Inline Bypass Switch Specifications
|
ML-BYPASS-M2000 Mylinking™ Network Packet Broker plus Inline Bypass Switch Functional Specifications |
||||
|
Network interface |
Module slot |
4 BYPASS or MONITOR module slots | ||
|
Number of inline links |
Supports protection for up to 16 1G/10G optical links or 8 40G/100G optical links. | |||
|
Monitor monitoring interface |
Supports a maximum of 64*1G/10GE monitoring interfaces or 16*40G/100G monitoring interfaces. | |||
|
Out-of-band management interface |
1*10/100/1000M Ethernet port; |
|||
|
Deployment mode |
Inline deployment |
Support |
||
|
SPAN deployment |
Support |
|||
|
System Functions |
Inline deployment mode |
Specific flow concatenation protection |
Support |
|
|
All flow series protection |
Support |
|||
|
Load balancing |
Support |
|||
|
Heartbeat detection |
Support |
|||
|
BYPASS switching |
Support |
|||
|
Traffic blocking |
Support |
|||
|
Traffic mirroring |
Support |
|||
|
SSL Proxy |
Support |
|||
|
SPAN deployment mode |
Basic traffic processing |
Traffic replication/aggregation/distribution |
Support |
|
|
Load balancing |
Support |
|||
|
Traffic filtering based on IP/protocol/port 5-tuple identifier |
Support |
|||
|
VLAN tagging/modification/deletion |
Support |
|||
|
Timestamping |
Support |
|||
|
Tunnel encapsulation stripping |
Support |
|||
|
Data Slicing |
Support |
|||
|
Tunneling Protocol Identification |
Support |
|||
|
Packet forwarding priority |
Support |
|||
|
Abnormal warning |
Support |
|||
|
Interface hot standby |
Support |
|||
|
Micro-burst measurement |
Support |
|||
|
Interface oscillation protection |
Support |
|||
|
Tunnel Encapsulation Output |
Support |
|||
|
Tunnel packet termination |
Support |
|||
|
Advanced traffic processing |
Bypass SSL Decryption |
Support |
||
|
Data deduplication |
Support |
|||
|
Data masking |
Support |
|||
|
Application layer protocol identification |
Support |
|||
|
Custom decapsulation |
Support |
|||
|
Flow shaping |
Support |
|||
|
Keyword matching |
Support |
|||
|
Tunnel encapsulation stripping |
Support |
|||
|
Long-lived connection unloading |
Support |
|||
|
Flow component observation |
Support |
|||
|
Diagnosis and monitoring |
Real-time monitoring |
Support |
||
|
Historical traffic query |
Support |
|||
|
Traffic capture |
Support |
|||
|
Traffic visualization detection |
Fundamental Analysis |
Supports summary statistical display based on basic information such as packet count, packet type distribution, session connection count, and packet protocol distribution. | ||
|
DPI In-depth Analysis |
It supports analysis of the proportion of transport layer protocols, the proportion of unicast, broadcast and multicast, the proportion of IP traffic, and the proportion of DPI applications.It supports the analysis and presentation of data content based on the sampling time and the volume of data.It supports data analysis and statistics based on session streams. | |||
|
Precise Fault Analysis |
Supports fault analysis and localization using traffic data from various perspectives, including:Packet transmission behavior analysis, data stream-level fault analysis, data packet-level fault analysis, security-related fault analysis, and network-related fault analysis. | |||
|
Processing capacity |
2.4Tbps |
|||
|
Manage |
CONSOLE Network Management |
Support |
||
|
IP/WEB Network Management |
Support |
|||
|
SNMP network management |
Support |
|||
|
TELNET/SSH network management |
Support |
|||
|
SYSLOG protocol |
Support |
|||
|
RADIUS or TADACS+ centralized authorization authentication |
Support |
|||
|
User authentication function |
Username and password authentication |
|||
|
Electric |
Rated power supply voltage |
AC-220V/DC-48V [Optional] |
||
|
Rated power frequency |
AC-50HZ |
|||
|
Rated input current |
AC-3A / DC-10A |
|||
|
Rated functional power |
Maximum 300W |
|||
|
Environment |
Operating temperature |
0-50℃ |
||
|
Storage temperature |
-20-70℃ |
|||
|
Operating humidity |
10%-95%, non-condensing |
|||
|
User Configuration |
Console configuration |
RS232 interface, 115200, 8, N, 1 |
||
|
Password authentication |
Support |
|||
|
Rack Size |
Rack space (U) |
2U 444mm*88mm*670mm |
||
6- Mylinking™ Network Packet Broker plus Inline Bypass Switch Application
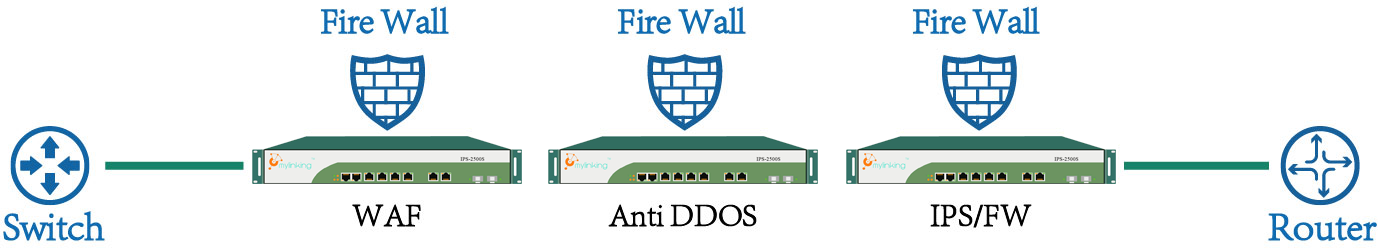
6.1 The Risk of Inline Security Equipment (IPS / FW)
The following is a typical IPS (Intrusion Prevention System), FW (Firewall) deployment mode, IPS / FW is deployed in series to the network equipment (routers, switches, etc.) between the traffic through the implementation of security checks, according to the corresponding security policy to determine the release or blocking the corresponding traffic, to achieve the effect of security defense.

The following is a typical IPS (Intrusion Prevention System), FW (Firewall) deployment mode, IPS / FW is deployed in series to the network equipment (routers, switches, etc.) between the traffic through the implementation of security checks, according to the corresponding security policy to determine the release or blocking the corresponding traffic, to achieve the effect of security defense.
6.2 Inline Link Series Equipment Protection

Mylinking™ Network Packet Broker plus Inline Bypass Switch is deployed in series between network devices (routers, switches, etc.), and the data flow between network devices no longer leads directly to IPS / FW, "Smart Inline Bypass Switch" to IPS / FW, when the IPS / FW due to overload, crash, software updates, policy updates and other conditions of failure, the "Smart Inline Bypass Switch" through intelligent heartbeat message detection Function of the timely discovery, and thus skip the faulty device, without interrupting the premise of the network, the rapid network equipment directly connected to protect the normal communication network; when the IPS / FW failure recovery, but also through intelligent heartbeat packets Detection of timely detection of the function, the original link to restore the security of enterprise network security checks.
Mylinking™ Network Packet Broker plus Inline Bypass Switch has a powerful intelligent heartbeat message detection function, the user can customize the heartbeat interval and the maximum number of retries, through a custom heartbeat message on the IPS / FW for health testing, such as send the heartbeat check message to the upstream / downstream port of IPS / FW, and then receive from the upstream / downstream port of IPS / FW, and judge whether the IPS / FW is working normally by sending and receiving the heartbeat message.
6.3 “SpecFlow” Policy Flow Inline Security Series Protection

When the security network device only needs to deal with the specific traffic in series security protection, through the Mylinking™ Network Packet Broker plus Inline Bypass Switch traffic per-processing function, through the traffic screening policy to connect the inline security device "Concerned" traffic is sent back directly to the network link, and the"concerned traffic section" is traction to the in-line safety device to perform safety checks. This will not only maintain the normal application of the safety detection function of the safety device, but also reduce the inefficient flow of the safety equipment to deal with the pressure; at the same time, the "Smart Inline Bypass Switch " can detect the working condition of the safety device in real time. The safety device works abnormally bypasses the data traffic directly to avoid disruption of network service.
The Mylinking™ Network Packet Broker plus Inline Bypass Switch can identify traffic based on the L2-L4 layer header identifier, such as VLAN tag, source / destination MAC address, source IP address, IP packet type, transport layer protocol port, protocol header key tag, and so on. A variety of matching conditions flexible combination can be defined flexibly to define the specific traffic types that are of interest to a particular security device and can be widely used for the deployment of special security auditing devices (RDP, SSH, database auditing, etc.).
6.4 Load balanced Inline Security Series Protection

The Mylinking™ Network Packet Broker plus Inline Bypass Switch is deployed in series between network devices (routers, switches, etc.). When a single IPS / FW processing performance is not sufficient to cope with network link peak traffic, The traffic load balancing function of the protector, the "bundling" of multiple IPS / FW cluster processing network link traffic, can effectively reduce the single IPS / FW processing pressure, improve the overall processing performance to meet the high bandwidth of the deployment environment Claim.
Mylinking™ Network Packet Broker plus Inline Bypass Switch has a powerful load balancing function, according to the frame VLAN tag, MAC information, IP information, port number, protocol and other information on the Hash load balancing distribution of traffic to ensure that each IPS / FW received data flow Session integrity.
6.5 Multi-series Inline Equipment Flow Traction Protection(Change Physical Serial Connection to Logical Parallel Connection)
In some key links (such as Internet outlets, server area exchange link) location is often due to the needs of security features and the deployment of multiple in-line security testing equipment (such as firewall, anti-DDOS attack equipment, WEB application firewall, intrusion prevention Equipment, etc.), multiple security detection equipment at the same time in series on the link to increase the link of a single point of failure, reducing the overall reliability of the network. And in the above-mentioned security equipment on-line deployment, equipment upgrades, equipment replacement and other operations, will cause the network for a long time service interruption and a larger project cut action to complete the successful implementation of such projects.
By deploying the Mylinking™ Network Packet Broker plus Inline Bypass Switch in a unified manner, the deployment mode of multiple security devices connected in series on the same link can be changed from "Physical Serial Connection Mode" to "Physical Parallel Connection but Logical Serial Connection Mode". This effectively reduces the sources of single point of failure on the serial link and improves the reliability of the link. At the same time, Mylinking™ Network Packet Broker plus Inline Bypass Switch can guide the link traffic on demand, achieving the same traffic security processing effect as the original serial connection mode.
More than one Inline Security device at the same time in series deployment diagram:
Mylinking™ Network Packet Broker plus Inline Bypass Switch Deployment Diagram:
(Change Pysical Serial Connection to Logical Parallel Connection)

6.6 Based on the Dynamic Policy of Traffic Inline Security Detection Protection
Mylinking™ Network Packet Broker plus Inline Bypass Switch, another advanced application scenario is based on the dynamic policy of traffic traction security detection protection applications, the deployment of the way as shown below:

Take the "Anti-DDoS attack protection and detection" security testing equipment, for example, through the front-end deployment of "Smart Bypass Switch" and then anti-DDOS protection equipment and then connected to the "Smart Bypass Switch", in the usual "Smart Bypass Switch"to the full amount of traffic wire-speed forwarding at the same time the flow mirror output to the" Anti-DDOS attack protection device", once detected for a server IP (or IP network segment) after the attack, "Anti-DDOS attack protection device" will generate the target traffic flow matching rules and send them to the "Smart Bypass Switch" through the dynamic policy delivery interface. The " Bypass Switch " can update the "traffic traction dynamic" after receiving the dynamic policy rules Rule pool "and immediately" rule hit the attack server traffic "traction to the" anti-DDoS attack protection and detection "equipment for processing, to be effective after the attack flow and then re-injected into the network.
The application scheme based on the "Smart Bypass Switch" is easier to implement than the traditional BGP route injection or other traffic traction scheme, and the environment is less dependent on the network and the reliability is higher.
"Smart Bypass Switch" has the following characteristics to support dynamic policy security detection protection:
1. "Smart Bypass Switch" to provide outside the rules based on WEBSERIVCE interface, easy integration with third-party security devices.
2. "Smart Bypass Switch" based on the hardware pure ASIC chip forwarding up to 100Gbps wire-speed packets without blocking switch forwarding, and "traffic traction dynamic rule library" regardless of the number.
3. "Smart Bypass Switch" built-in professional BYPASS function, even if the protector itself failure, can also bypass the original serial link immediately, does not affect the original link of normal communication.
6.7 Inline Serial Traffic Mirroring for Out-of-band Security(Inline + SPAN)
The Mylinking™ Network Packet Broker plus Inline Bypass Switch is typically deployed in a customer's IT network or cloud platform network to provide in-line protection for WAF/IPS devices and the original link. Users may also have additional requirements for testing, verification, or deployment of bypass monitoring devices, necessitating the acquisition of traffic data on this link.
Therefore, using the traffic mirroring function of the Mylinking™ Network Packet Broker plus Inline Bypass Switch, the traffic of the inline serial link can be mirrored from the monitor port, as shown in the following figure:
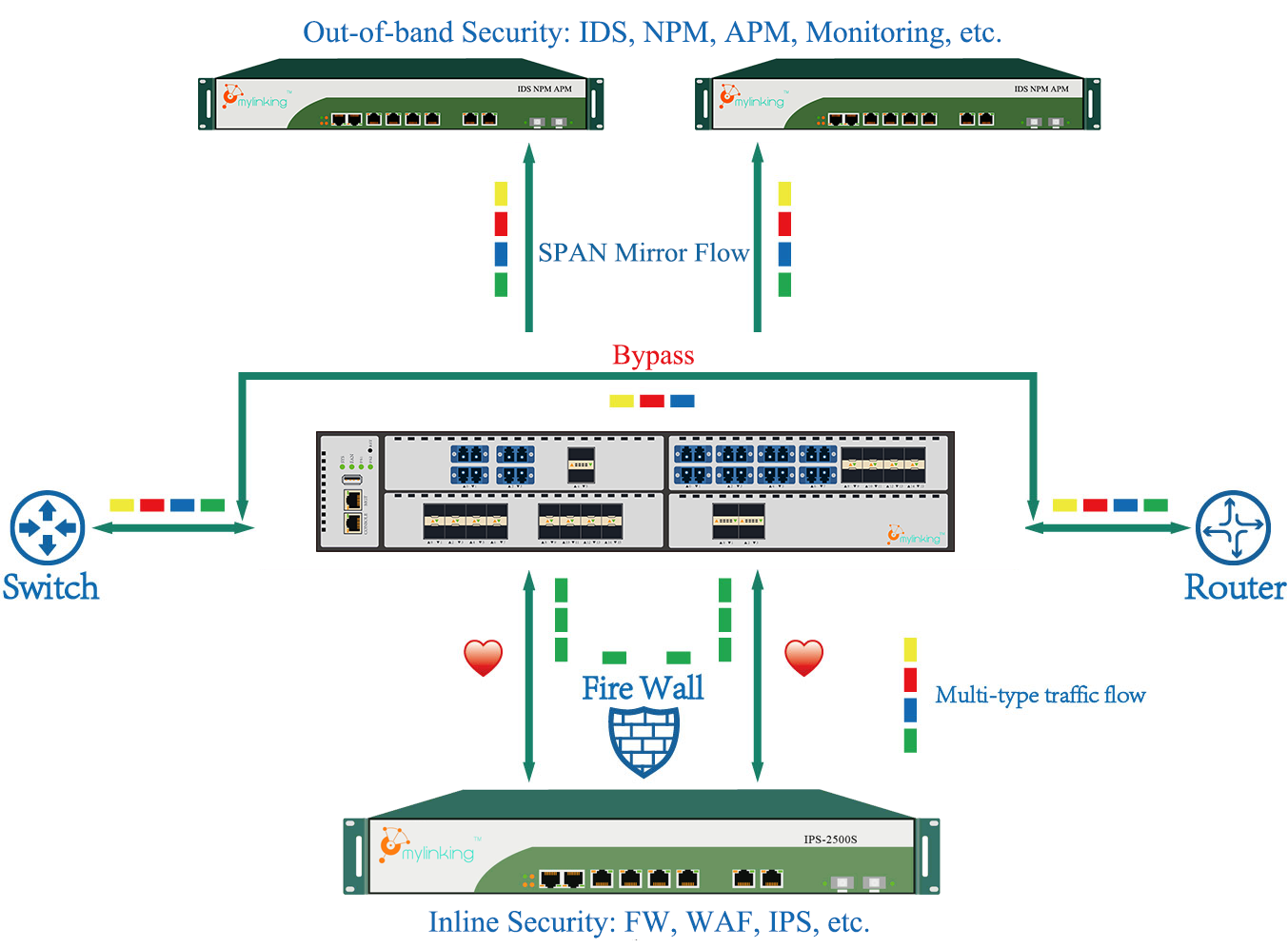
The diagram below illustrates an extended application scenario of inline link traffic and switch mirrored port traffic. This allows for inline link traffic protection without being affected by switch mirrored port traffic. The IDS analysis system can simultaneously acquire both inline link traffic and switch mirrored port traffic. The deployment method is shown in the diagram below:

6.8 Data/Packet De-duplication Application

As shown in the application deployment structure above, to ensure the integrity of the original data collection along the entire link, some identical data packets may be collected multiple times within a single path. This leads to increased false alarms and retransmissions in the backend system, increasing the performance overhead of the analysis system and affecting the accuracy and effectiveness of the analysis. Based on the solution, first, duplicate data packets which are deduplicated in different capturing nodes. Only one data packet is forwarded to the backend NPM network performance analysis system and APM application performance analysis system, thereby saving the performance of the analysis system and improving the efficiency and accuracy of analysis.
6.9 Data/Packet VLAN Tagging Application

In the network environment shown in the diagram above, the solution is used to tag the label raw data from different network devices and link nodes. When abnormal traffic or data packets occur in the network, the backend analysis equipment can quickly and accurately locate the source of the abnormal data by tracing back based on the data labels.
6.10 Network Traffic Unified Schedule Application

In the network environment shown in the diagram above, multiple 10GE, 25GE, 40GE and 100GE source link data are fully input into the Mylinking™ Network Packet Broker plus Inline Bypass Switch using optical splitting or port mirror. Then, filtering and traffic splitting are used to output different service data traffic to different backend out-of-band network monitoring and security system devices. When network packet anomalies or abnormal traffic fluctuations require manual intervention, real-time packet capture and analysis of the original data packets can be performed immediately to help users quickly analyze and locate the fault.
6.11 Network Traffic Data Visibility Analysis Application

It can present any data detected and captured in a multi-dimensional and multi-perspective manner through a user-friendly graphic and text interactive interface, including traffic composition structure, application protocol distribution, traffic distribution of all network nodes, data transmission path, abnormal event detection, precise location of network element/link faults, message interaction status, traffic development trend and other aspects for monitoring and analysis, so as to establish a comprehensive, visible and controllable overall data collection and security platform for enterprise networks.










