Network Packet Broker (NPB) is a switch like networking device that ranges in size from portable devices to 1U and 2U unit cases to large cases and board systems. Unlike a switch, the NPB does not change the traffic that flows through it in any way unless explicitly instructed. NPB can receive traffic on one or more interfaces, perform some predefined functions on that traffic, and then output it to one or more interfaces.
These are often referred to as any-to-any, many-to-any, and any-to-many port mappings. The functions that can be performed range from simple, such as forwarding or discarding traffic, to complex, such as filtering information above layer 5 to identify a particular session. Interfaces on NPB can be copper cable connections, but are usually SFP/SFP + and QSFP frames, which allow users to use a variety of media and bandwidth speeds. NPB's feature set is built on the principle of maximizing the efficiency of network equipment, particularly monitoring, analysis, and security tools.
What functions does the Network Packet Broker provide?
NPB's capabilities are numerous and may vary depending on the brand and model of device, although any package agent worth his salt will want to have a core set of capabilities. Most NPB (the most common NPB) functions at OSI layers 2 through 4.
In general, you can find the following features on the NPB of L2-4: traffic (or specific parts of it) redirection, traffic filtering, traffic replication, protocol stripping, packet slicing (truncation), starting or terminating various network tunnel protocols, and load balancing for traffic. As expected, L2-4's NPB can filter VLAN, MPLS labels, MAC addresses (source and target), IP addresses (source and target), TCP and UDP ports (source and target), and even TCP flags, as well as ICMP, SCTP, and ARP traffic. This is by no means a feature to be used, but rather provides an idea of how NPB operating at layers 2 through 4 can separate and identify traffic subsets. A key requirement that customers should look for in NPB is a non-blocking backplane.
Network packet Broker need to be able to meet the full traffic throughput of each port on the device. In the chassis system, the interconnection with the backplane must also be able to meet the full traffic load of the connected modules. If the NPB drops the packet, these tools will not have a complete understanding of the network.
Although the vast majority of NPB is based on ASIC or FPGA, due to the certainty of packet processing performance, you will find many integrations or CPUs acceptable (via modules). The Mylinking™ Network Packet Brokers(NPB) are based on ASIC solution. This is usually a feature that provides flexible processing and therefore cannot be done purely in hardware. These include packet deduplication, timestamps, SSL/TLS decryption, keyword search, and regular expression search. It is important to note that its functionality depends on CPU performance. (For example, regular expression searches of the same pattern can yield very different performance results depending on traffic type, matching rate, and bandwidth), so it is not easy to determine before actual implementation.
If CPU-dependent features are enabled, they become a limiting factor in the overall performance of the NPB. The advent of cpus and programmable switching chips, such as Cavium Xpliant, Barefoot Tofino and Innovium Teralynx, also formed the basis of an expanded set of capabilities for next-generation network packet agents, These functional units can handle traffic above L4 (often referred to as L7 packet agents). Among the advanced features mentioned above, keyword and regular expression search are good examples of next-generation capabilities. The ability to search packet payloads provides opportunities to filter traffic at the session and application levels, and provides finer control over an evolving network than the L2-4.
How does Network Packet Broker fit into the infrastructure?
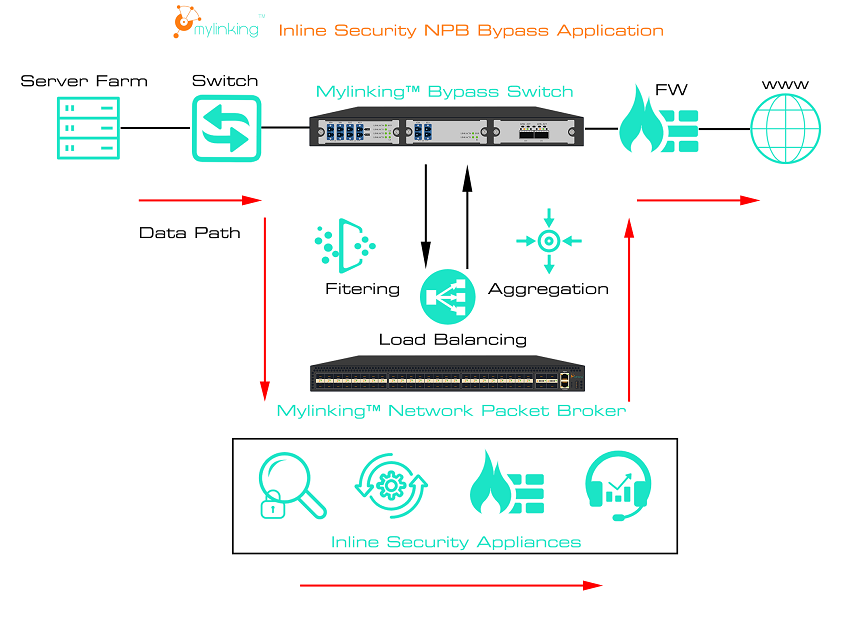
The NPB can be installed into a network infrastructure in two different ways:
1- Inline
2- Out-of-band.
Each approach has advantages and disadvantages and enables traffic manipulation in ways that other approaches cannot. The inline network packet broker has real-time network traffic that traverses the device on its way to its destination. This provides the opportunity to manipulate traffic in real time. For example, when adding, modifying, or deleting VLAN tags or changing destination IP addresses, traffic is copied to a second link. As an inline method, NPB can also provide redundancy for other inline tools, such as IDS, IPS, or firewalls. NPB can monitor the status of such devices and dynamically re-route traffic to hot standby in the event of a failure.
It provides great flexibility in how traffic is processed and replicated to multiple monitoring and security devices without affecting the real-time network. It also provides unprecedented network visibility and ensures that all devices receive a copy of the traffic needed to properly handle their responsibilities. It not only ensures that your monitoring, security, and analysis tools get the traffic they need, but also that your network is secure. It also ensures that the device does not consume resources on unwanted traffic. Perhaps your network analyzer does not need to record backup traffic because it takes up valuable disk space during the backup. These things are easily filtered out of the analyzer while preserving all the other traffic for the tool. Maybe you have an entire subnet that you want to keep hidden from some other system; again, this is easily removed on the selected output port. In fact, a single NPB can process some traffic links inline while processing other out-of-band traffic.
Post time: Mar-09-2022