There’s no doubt that 5G Network is important, promising the high speeds and unparalleled connectivity that are required to unleash the full potential of the “Internet of Things” also as "IoT" — the ever-growing network of web-connected devices—and artificial intelligence. For example, Huawei's 5G Network could prove critical to economic competitiveness, but not only will a race to install the system end up backfiring, there is also reason to think twice about the claims of China’s Huawei that it alone can shape our technological future.
Internet of things intelligent terminal security threat Security threats
1) weak password problem exists in intelligent terminal devices of Internet of things;
2) the operating system of intelligent terminal equipment of the Internet of things, built-in Web applications, databases, etc. have security vulnerabilities and are used to steal data, launch DDoS attacks, send spam or be manipulated to attack other networks and other serious security events;
3) weak identity authentication of intelligent terminal devices of Internet of things;
4) Internet of things smart terminal devices are implanted with malicious code or become botnets.
Security threat characteristics
1) there are a large number and types of weak passwords in intelligent terminal devices of Internet of things, which cover a wide range;
2) after the Internet of things intelligent terminal device is maliciously controlled, it can directly affect personal life, property, privacy and life security;
3) malicious use of simple;
4) it is difficult to reinforce the intelligent terminal equipment of Internet of things in the later stage, so security issues should be considered in the design and development stage;
5) the intelligent terminal devices of the Internet of things are widely distributed and used in different scenarios, so it is difficult to carry out unified upgrade and patch reinforcement;
6) malicious attacks can be carried out after identity forging or forgery;7) used for stealing data, launching DDoS attacks, sending spam or being manipulated to attack other networks and other serious security events.
Analysis on security control of intelligent terminal of Internet of things
During the design and development stage, the intelligent terminal of Internet of things should consider security control measures simultaneously.Perform safety protection test synchronously before terminal production release;Synchronize firmware vulnerability update management and intelligent terminal security monitoring during the terminal release and use phase.Specific Internet of things terminal security control analysis is as follows:
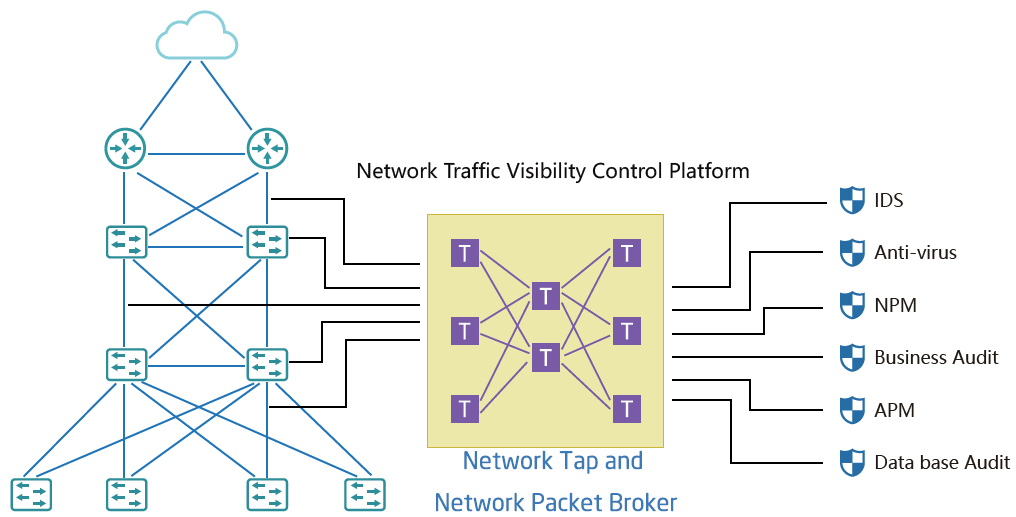
1) in view of the wide distribution and large number of intelligent terminals in the Internet of things, the Internet of things should carry out virus detection and detection on the network side.
2) for information retention of intelligent terminals of the Internet of things, relevant specifications should be established to limit the types, duration, methods, encryption means and access measures of information retention.
3) the identity authentication strategy of Internet of things intelligent terminal should establish strong identity authentication measures and perfect password management strategy.
4) before the production and release of Internet of things intelligent terminals, security testing should be done, firmware updates and vulnerability management should be done timely after the release of terminals, and network access permission should be granted if necessary.
5) build a security inspection platform for intelligent terminals of the Internet of things or build corresponding security monitoring means to detect abnormal terminals, isolate suspicious applications or prevent the spread of attacks.
Internet of things cloud service security threats
1) Data leakage;
2) Login credentials stolen and identity authentication forged;
3) API (application program programming interface) is attacked by a malicious attacker;
4) System vulnerability utilization;
5) System vulnerability utilization;
6) Malicious personnel;
7) Permanent data loss of the system;
8) Threat of denial of service attack;
9) Cloud services share technologies and risks.
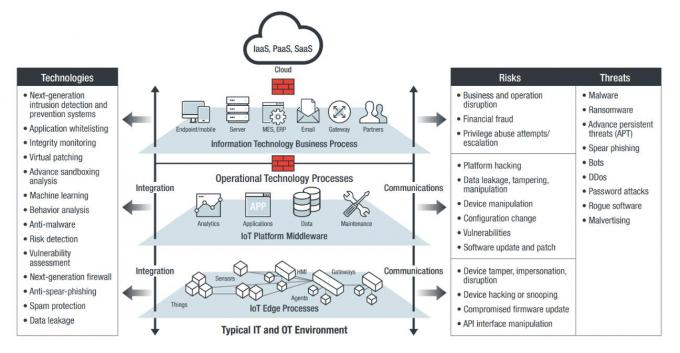
Characteristics of security threats
1) Large amount of leaked data;
2) Easy to form APT (advanced persistent threat) attack target;
3) The value of leaked data is high;
4) Great impact on individuals and society;
5) Internet of things identity forgery is easy;
6) If the credential control is not proper, the data cannot be isolated and protected;
7) The Internet of things has many API interfaces, which are easy to be attacked by malicious attackers;
8) The types of Internet of things API interfaces are complex and the attacks are diversified;
9) The vulnerability of the cloud service system of the Internet of things has a great impact after being attacked by a malicious attacker;
10) Malicious ACTS of internal personnel against data;
11) Threat of attack by outsiders;
12) Cloud data damage will cause damage to the entire Internet of things system
13) Affecting the national economy and people's livelihood;
14) Causing abnormal services in the Internet of things system;
15) Virus attack caused by sharing technology.
Post time: Dec-01-2022